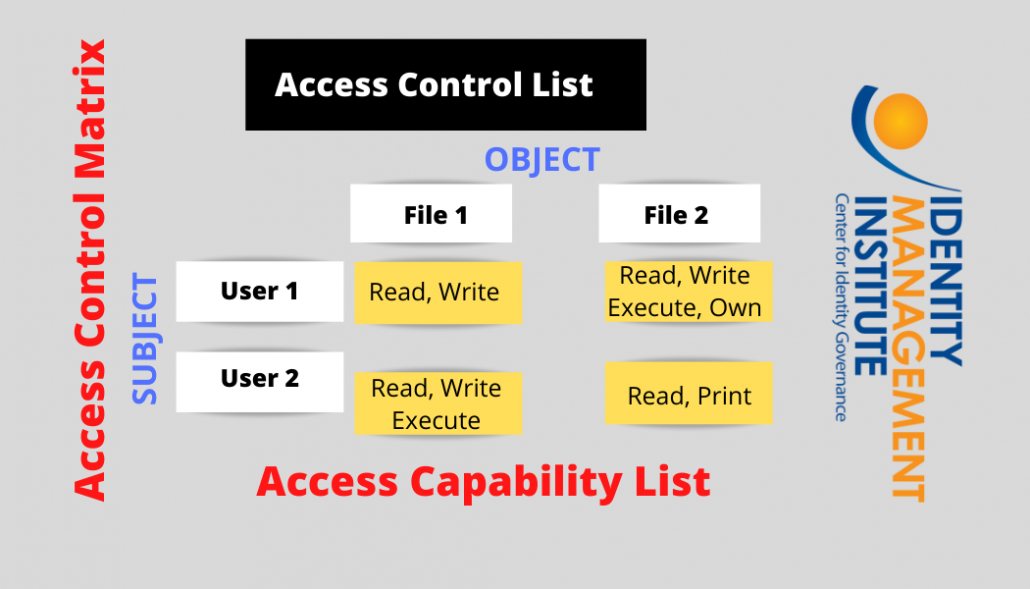
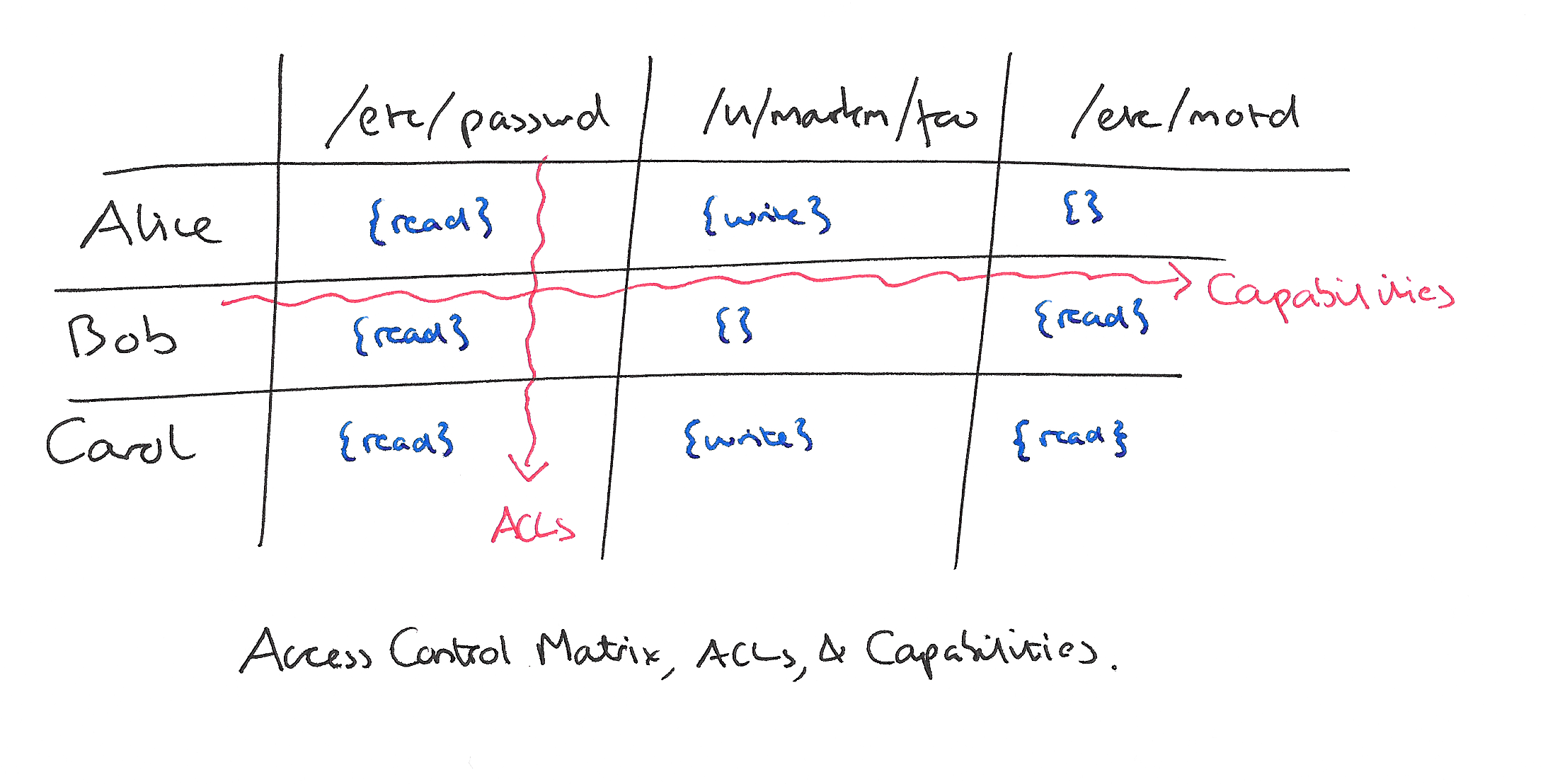
1. An access control matrix, and its access control list and capability... | Download Scientific Diagram

1. An access control matrix, and its access control list and capability... | Download Scientific Diagram
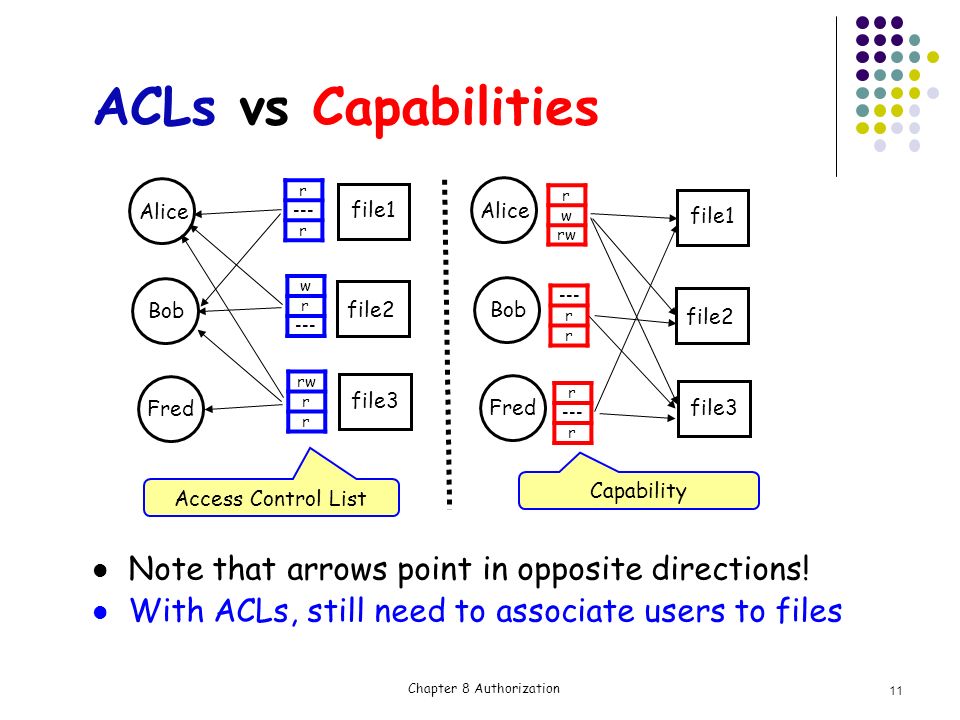
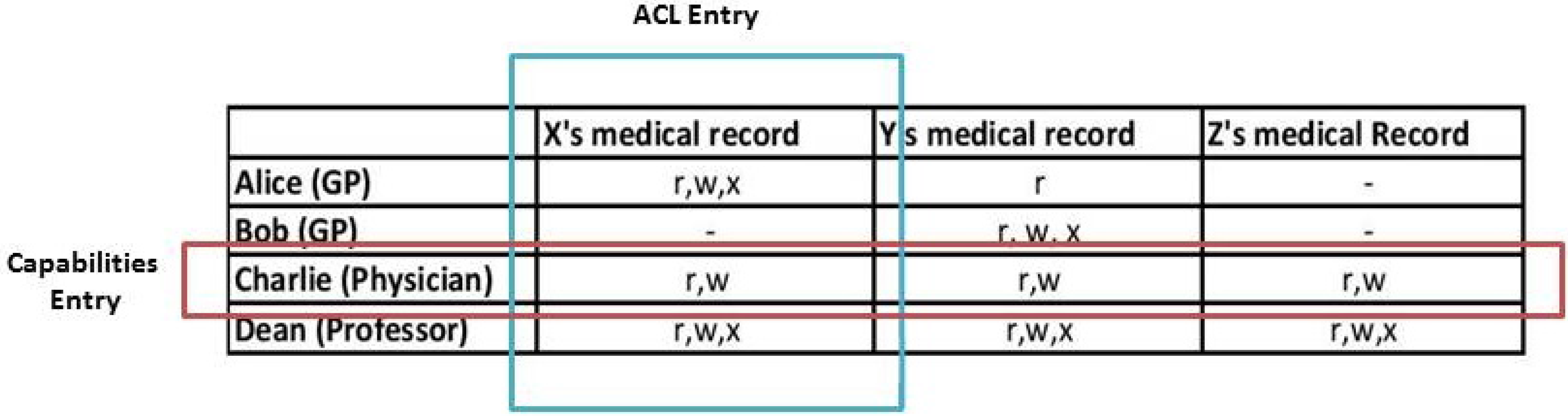
Chapter 8 Authorization Access control matrix Multilevel Security Multilateral security Covert channel Inference control CAPTCHA Firewalls IDS. - ppt download

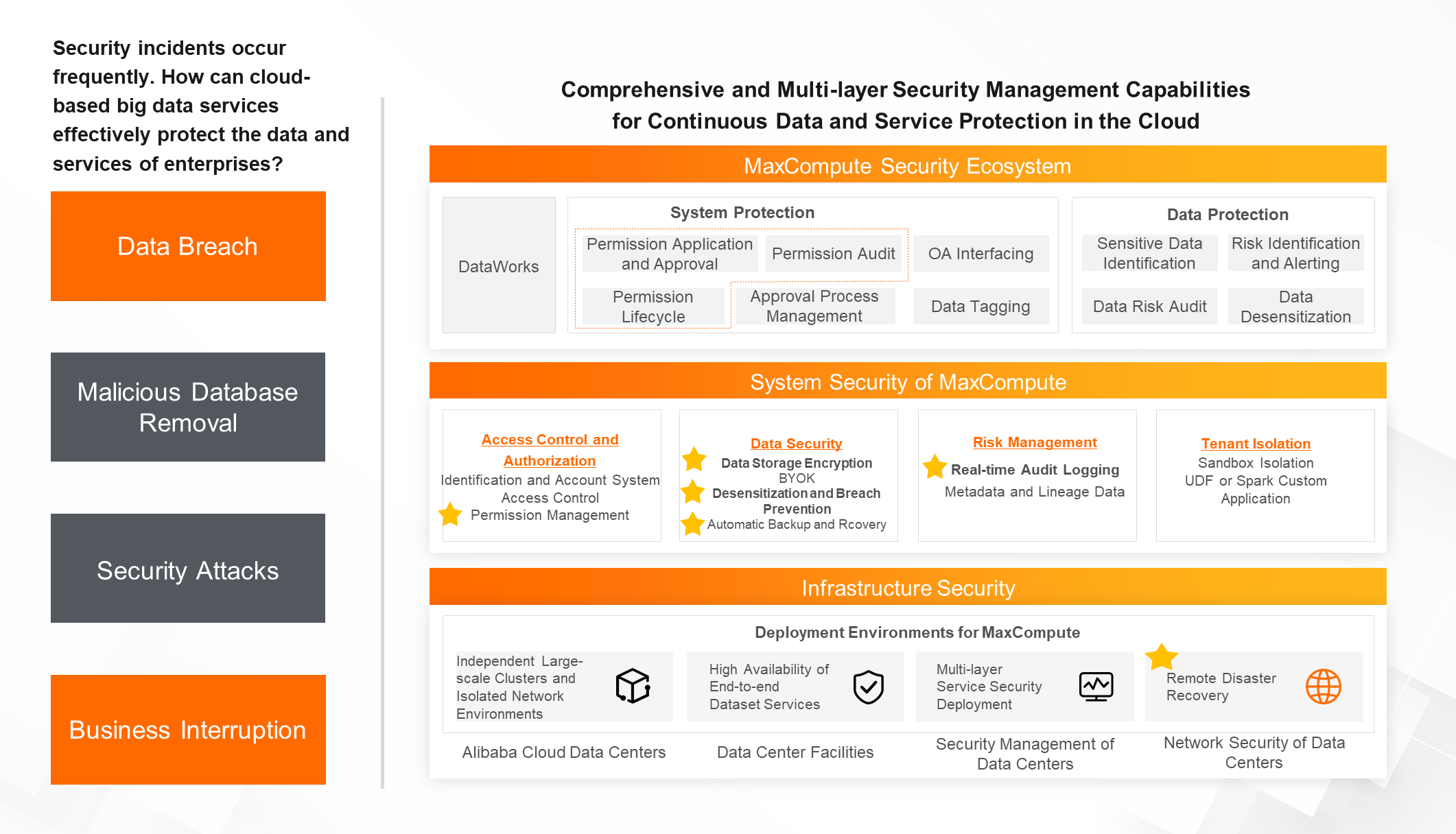
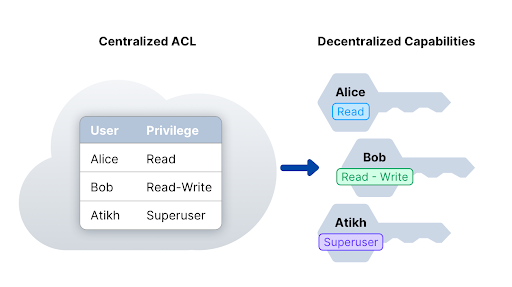
A capability-based security approach to manage access control in the Internet of Things - ScienceDirect

A capability-based security approach to manage access control in the Internet of Things - ScienceDirect

provides examples of potential usage of capability based authorization... | Download Scientific Diagram