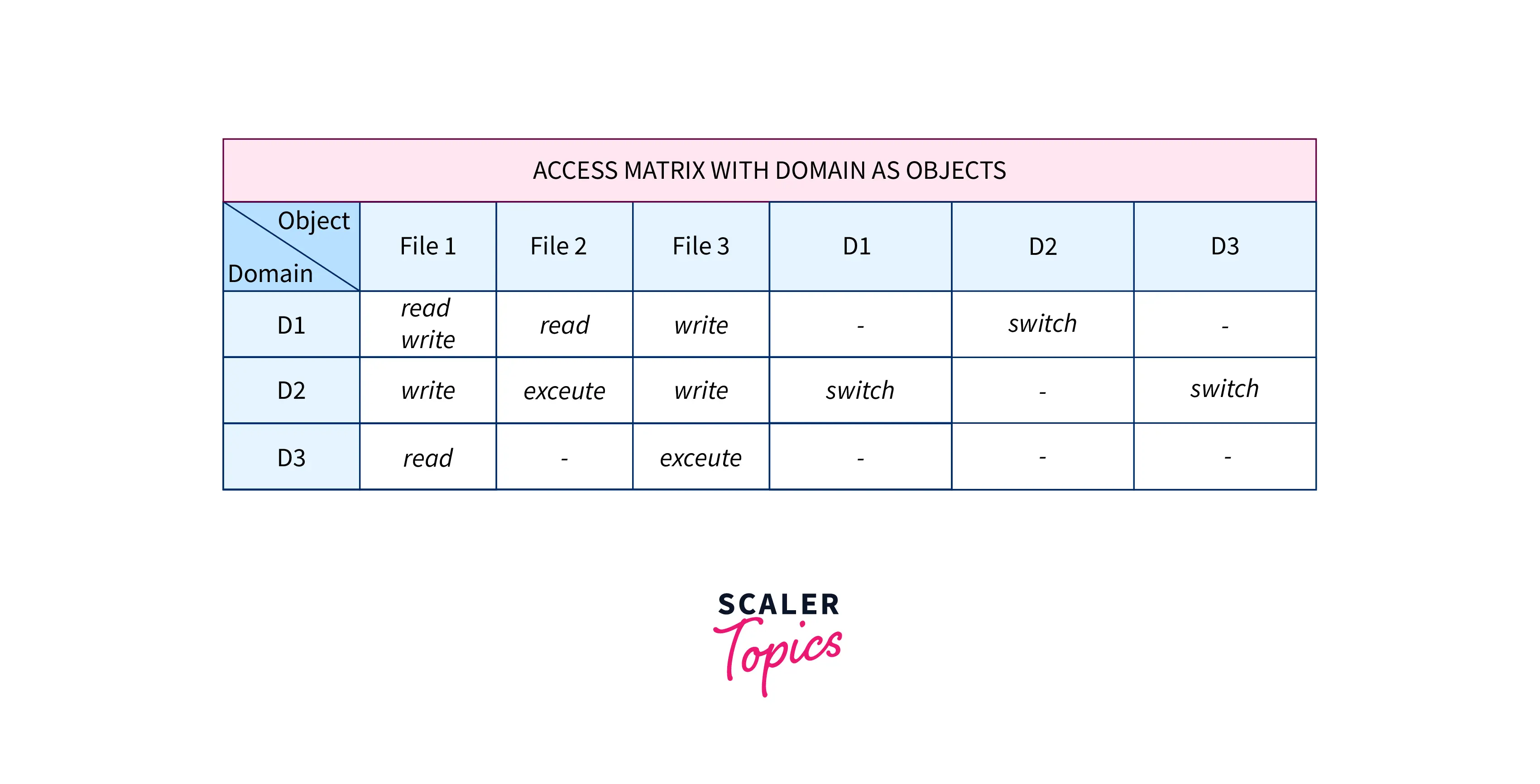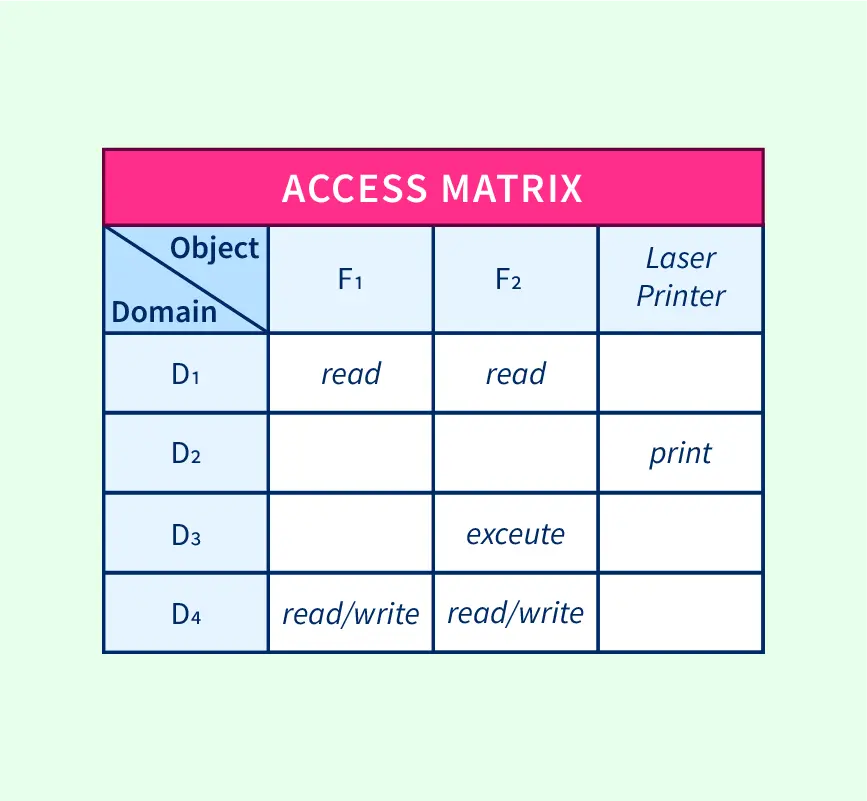
Semantic Technology Access Control Using DatasetsAI3:::Adaptive InformationAI3:::Adaptive Information
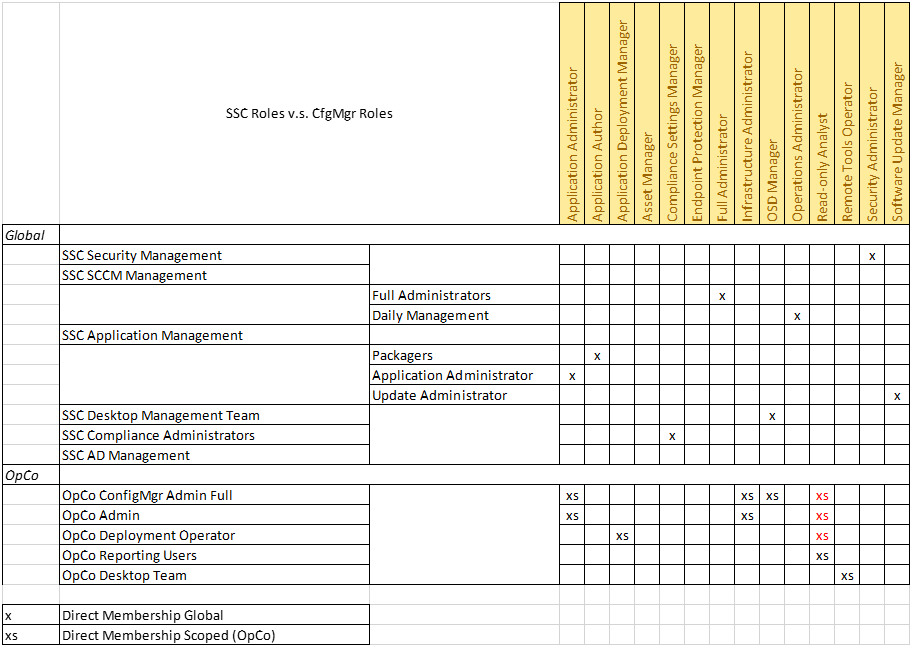
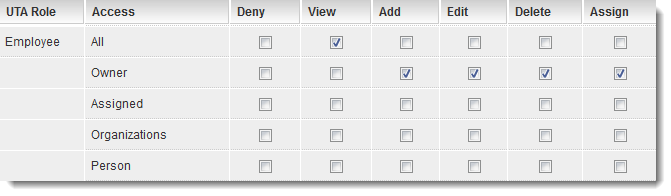
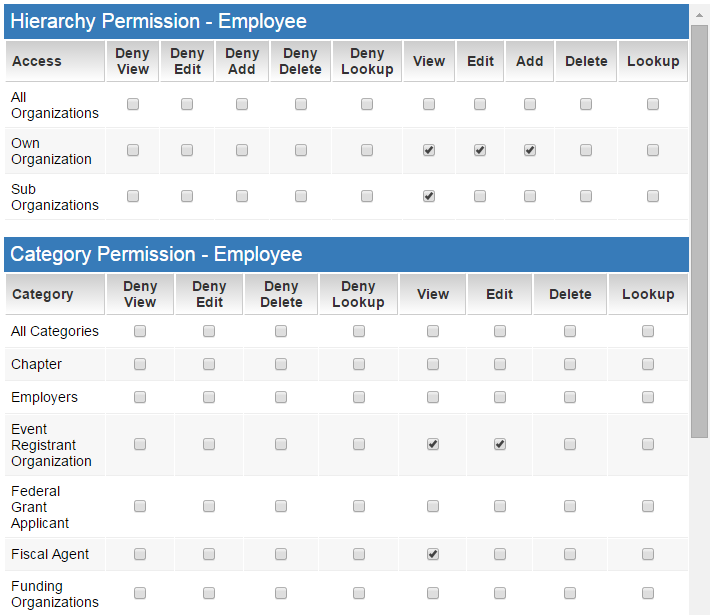
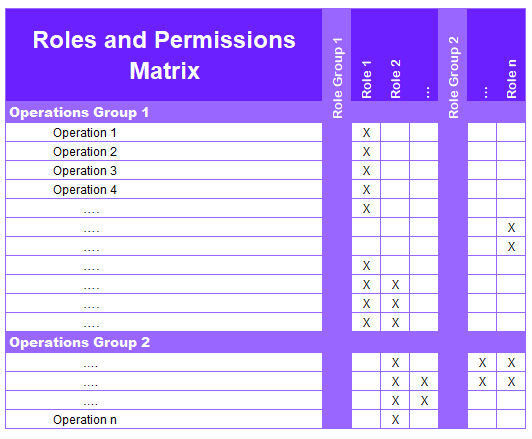
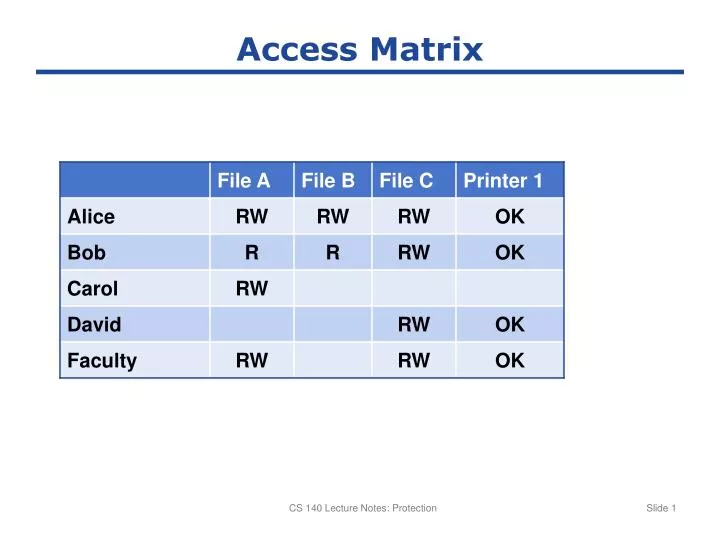
Role Based Access Control in ConfigMgr 2012: Part 3 Mapping OpCo roles to ConfigMgr roles - Modern Workplace Blog
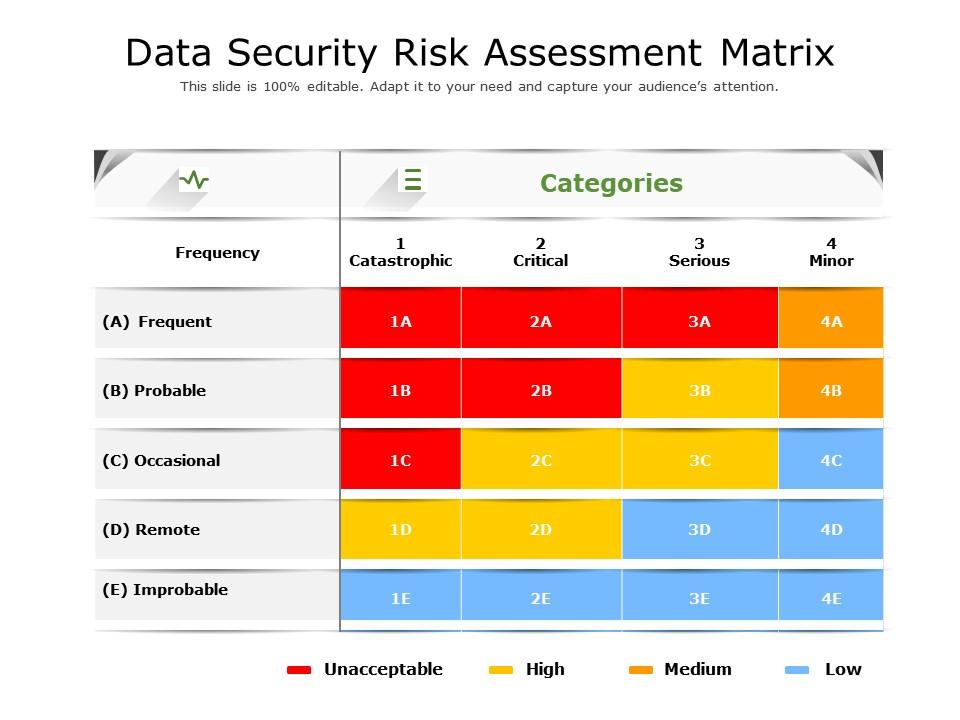
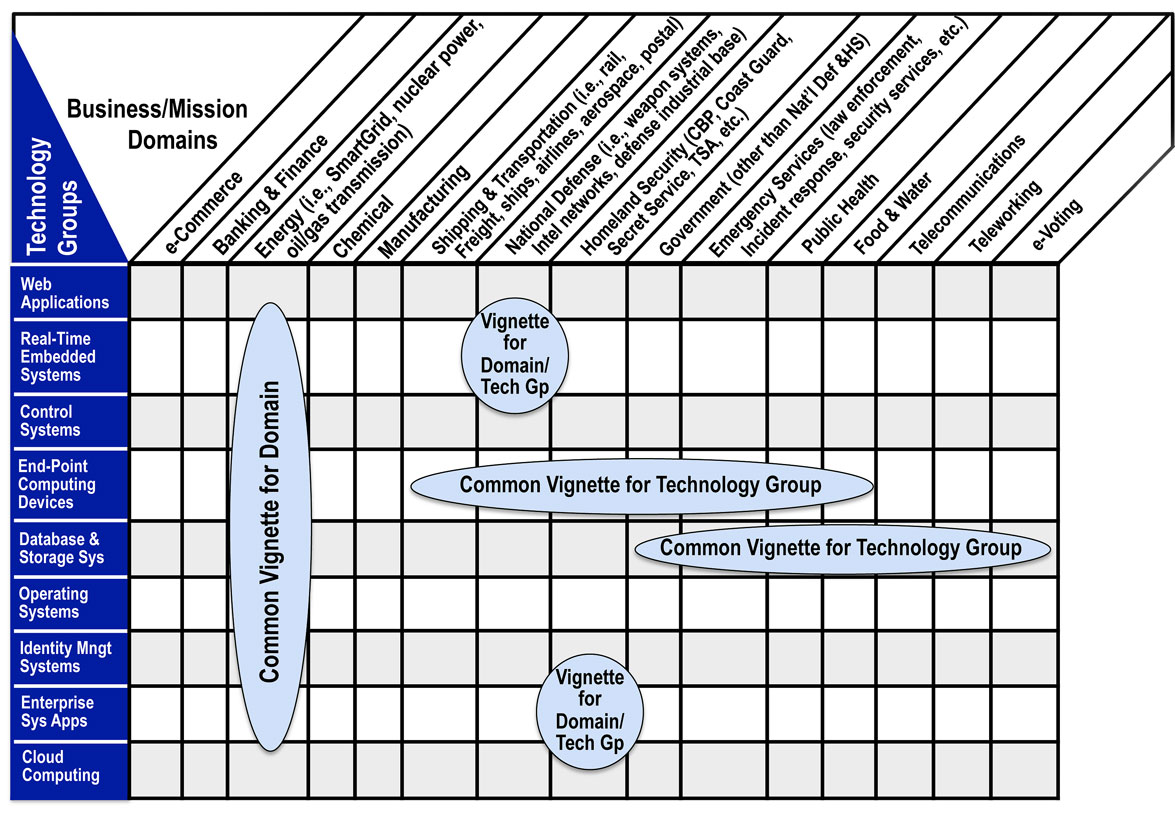
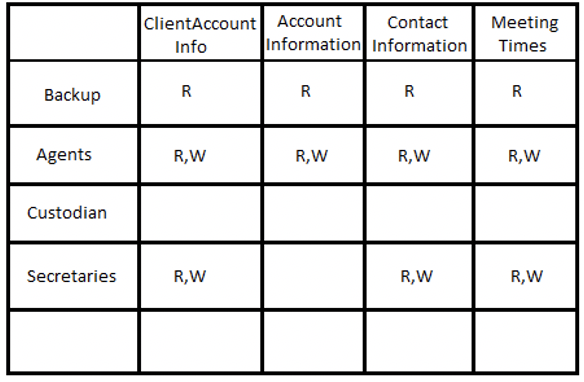
Data Security Risk Assessment Matrix | Presentation Graphics | Presentation PowerPoint Example | Slide Templates

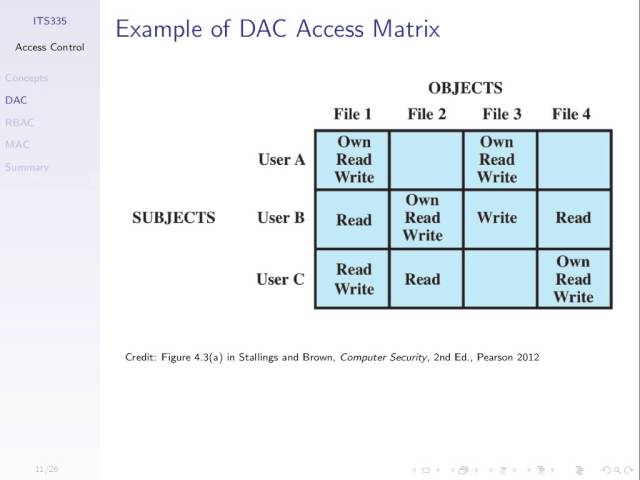
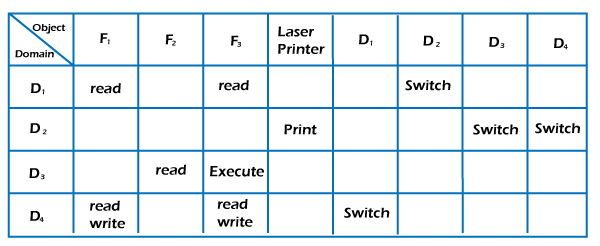
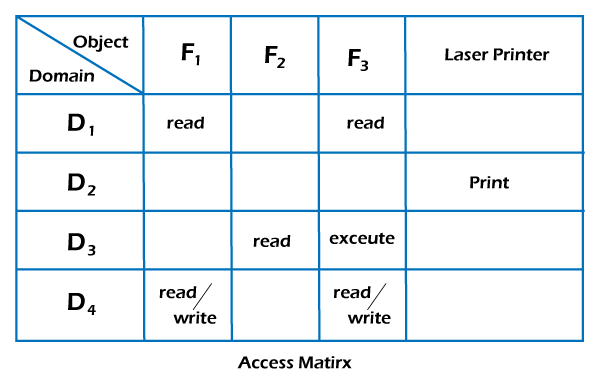
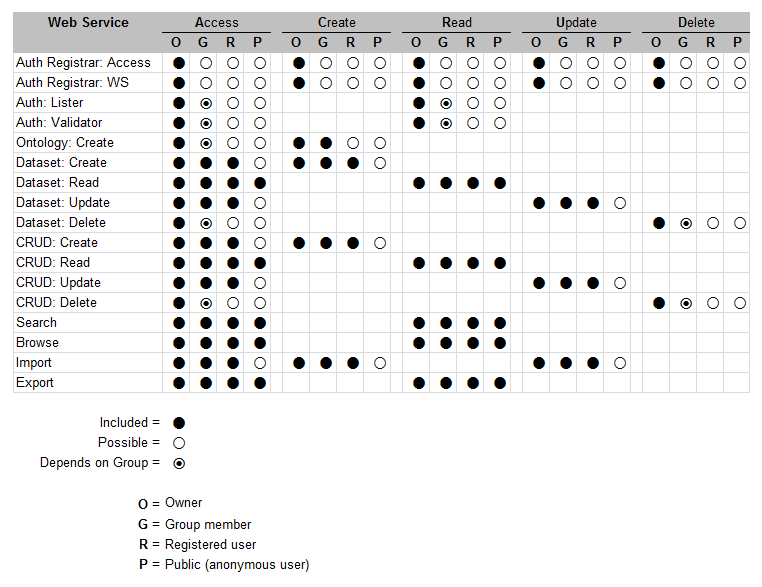
1. An access control matrix, and its access control list and capability... | Download Scientific Diagram