Process to generate security policy tests from an access control model | Download Scientific Diagram
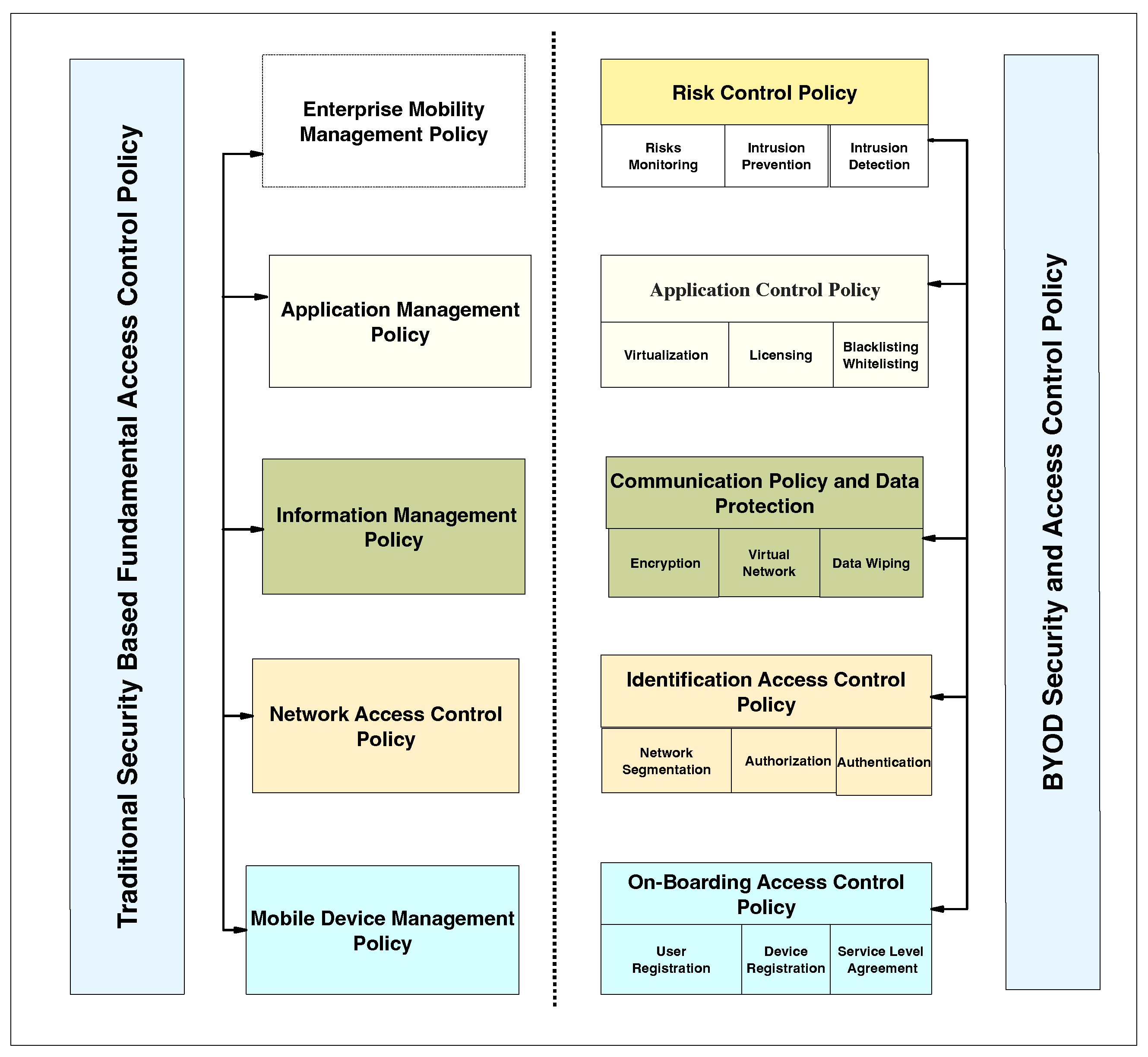
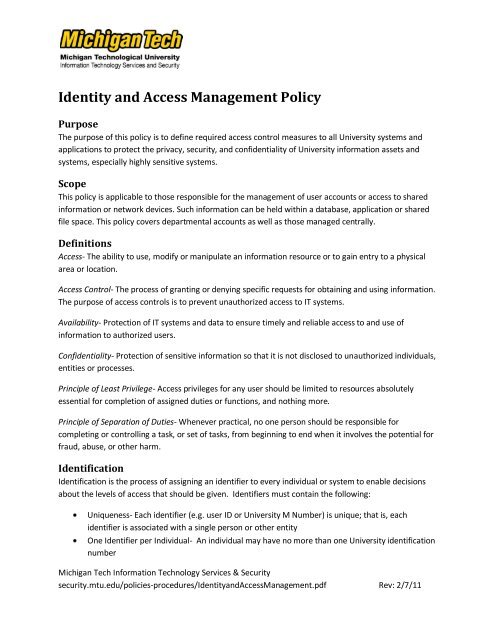
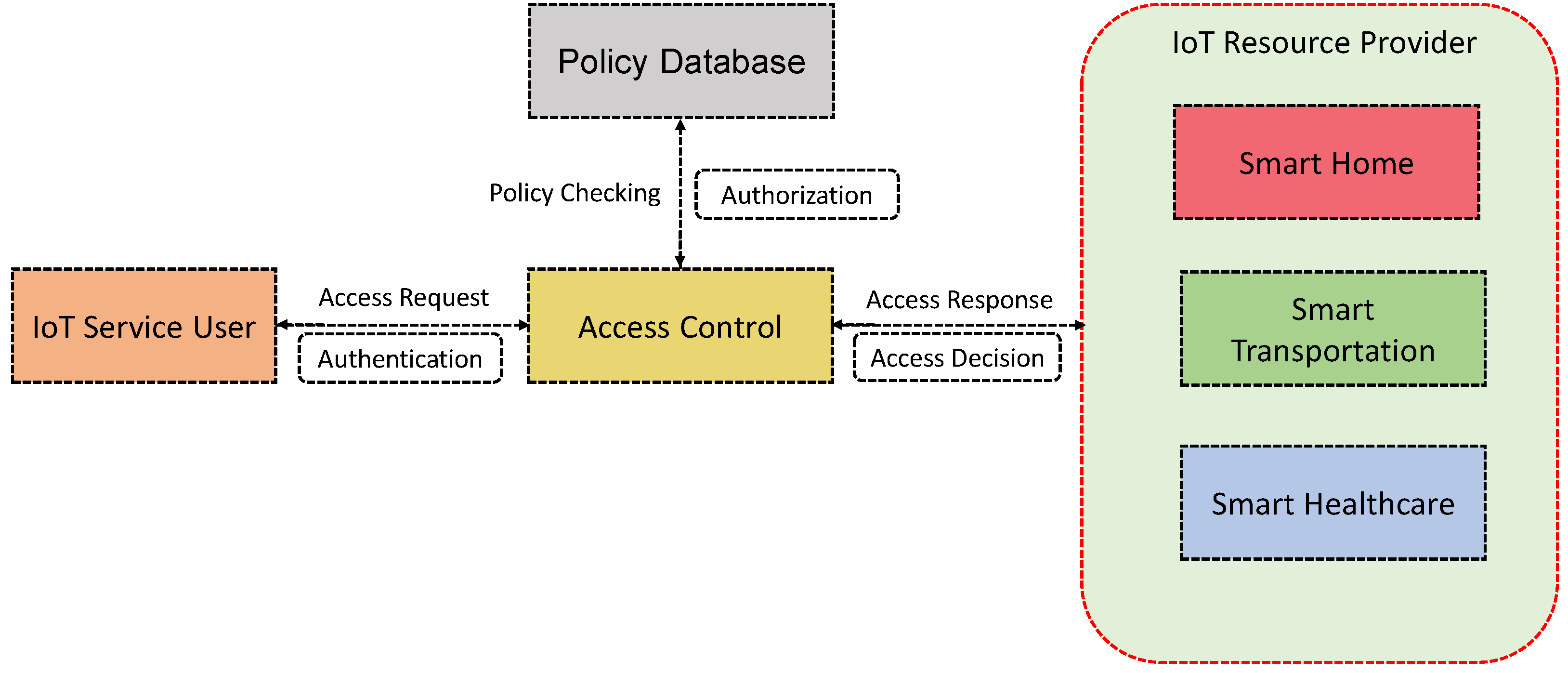
Applied Sciences | Free Full-Text | Systematic Literature Review on Security Access Control Policies and Techniques Based on Privacy Requirements in a BYOD Environment: State of the Art and Future Directions
Facility Physical Security and Access Control Pr The County of San Bernardino Department of Behavioral Health


![Access Control Policy & Procedures Template [w/ Examples] Access Control Policy & Procedures Template [w/ Examples]](https://ipkeys.com/wp-content/uploads/2023/02/access-control-policy-1024x635.jpeg)







![Access Control Policy [ISO 27001 templates] Access Control Policy [ISO 27001 templates]](https://advisera.com/wp-content/uploads//sites/5/2021/08/A.9.1_Access_Control_Policy_Premium_Preview_EN.png)