Ad-hoc im Fokus der Investoren! Versteckte Botschaft – das Startup und die weltweite Nr. 2! - 17.05.23 - News - ARIVA.DE
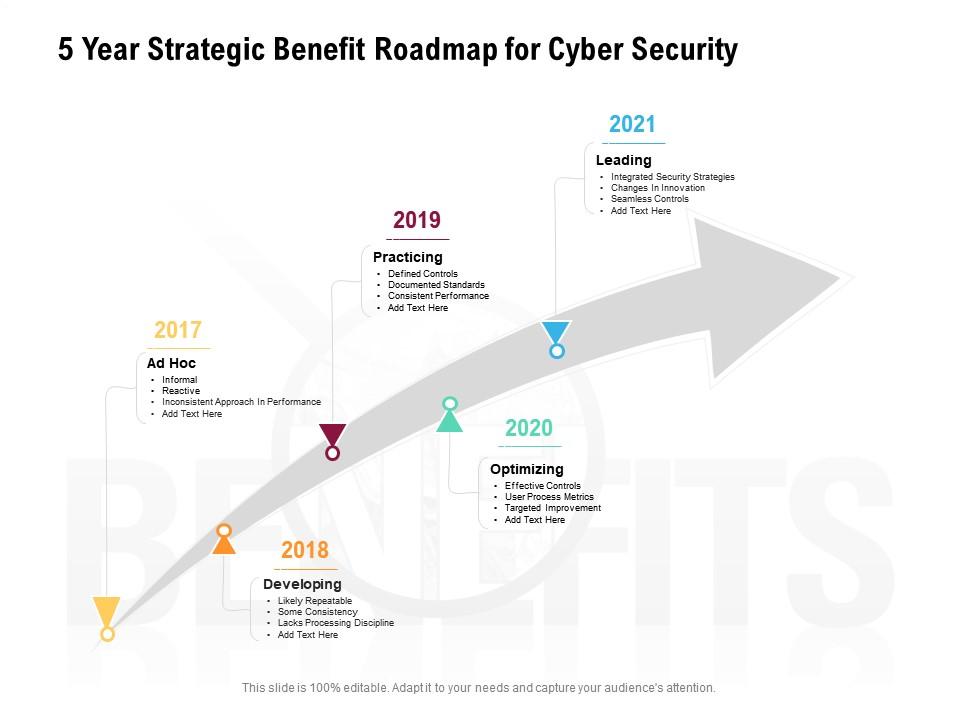
Strategischer 5-Jahres-Vorteilplan für Cybersicherheit | PowerPoint-Foliendiagramme | Themen für PPT | Grafische Ideen für Präsentationen
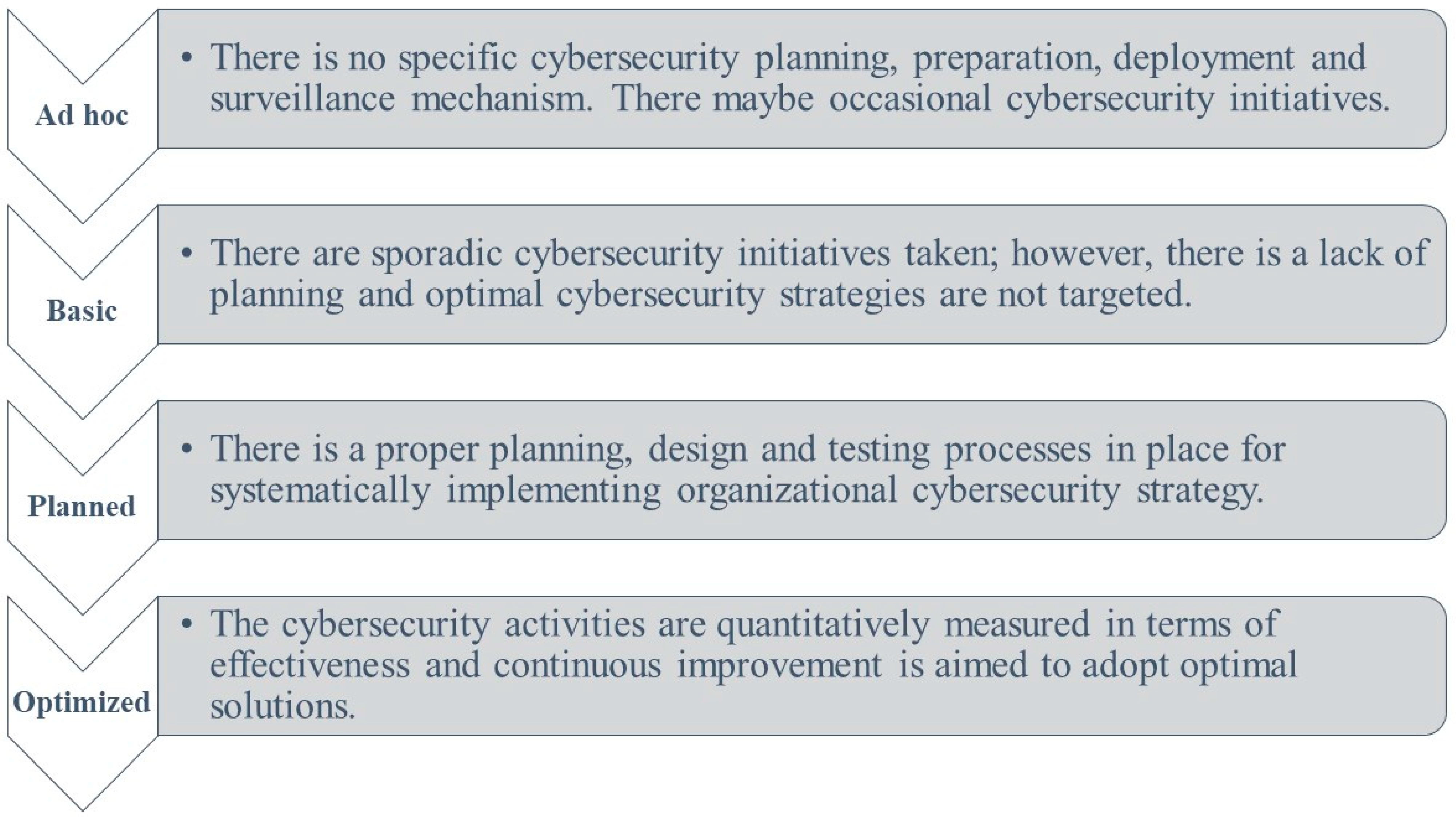
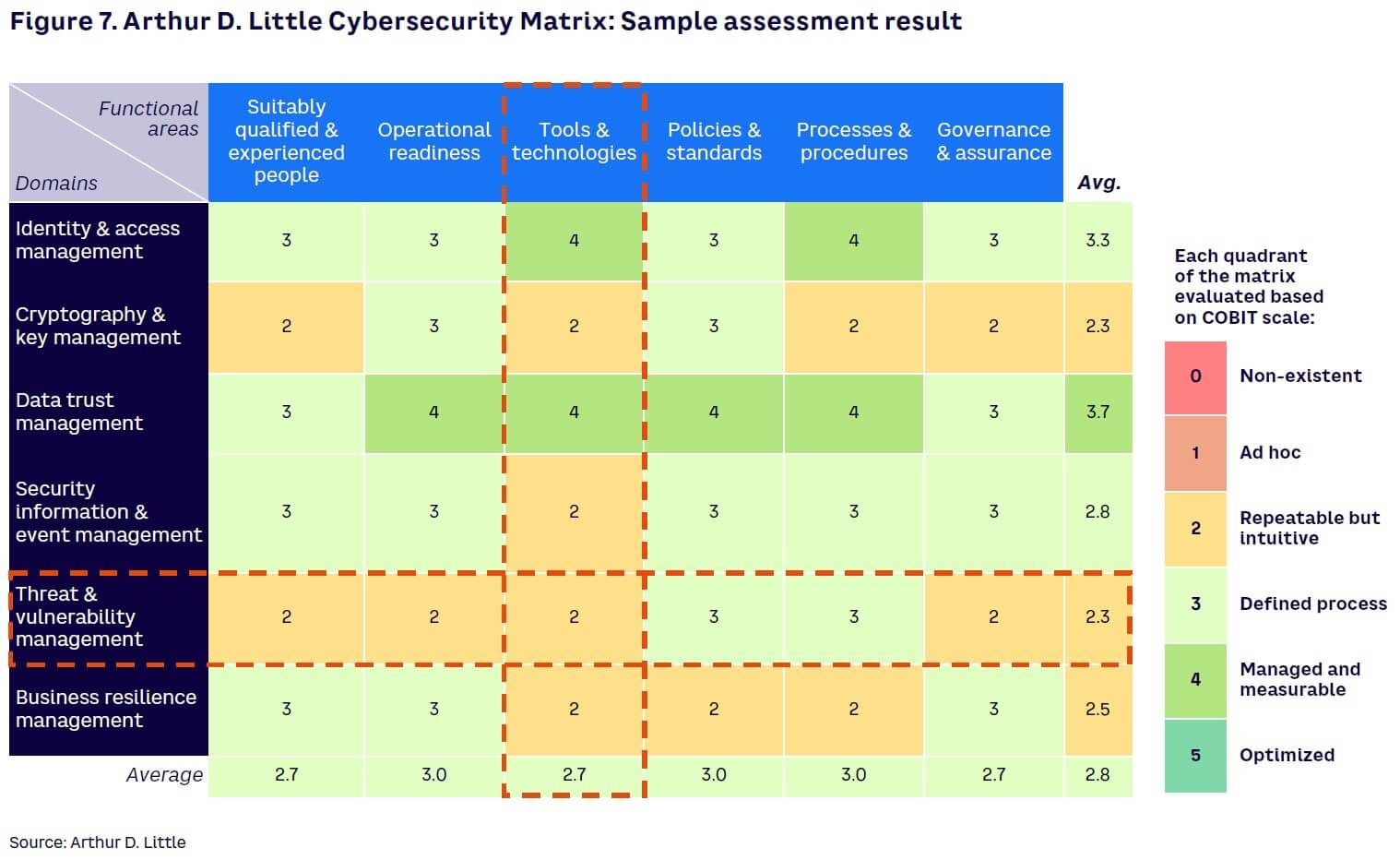
Sensors | Free Full-Text | Digital Transformation and Cybersecurity Challenges for Businesses Resilience: Issues and Recommendations

Showing military ad-hoc network in which soldiers are communicating... | Download Scientific Diagram

Cyber Security Competence Center: Voice richtet ein unabhängiges Cyber Security Competence Center ein - computerwoche.de
.jpg)
Call for expression of interest for the first ad hoc working group on cybersecurity certification — ENISA

L26: Security in Adhoc Wireless Network | Requirements, Issues, Challenges in Security Provisioning - YouTube