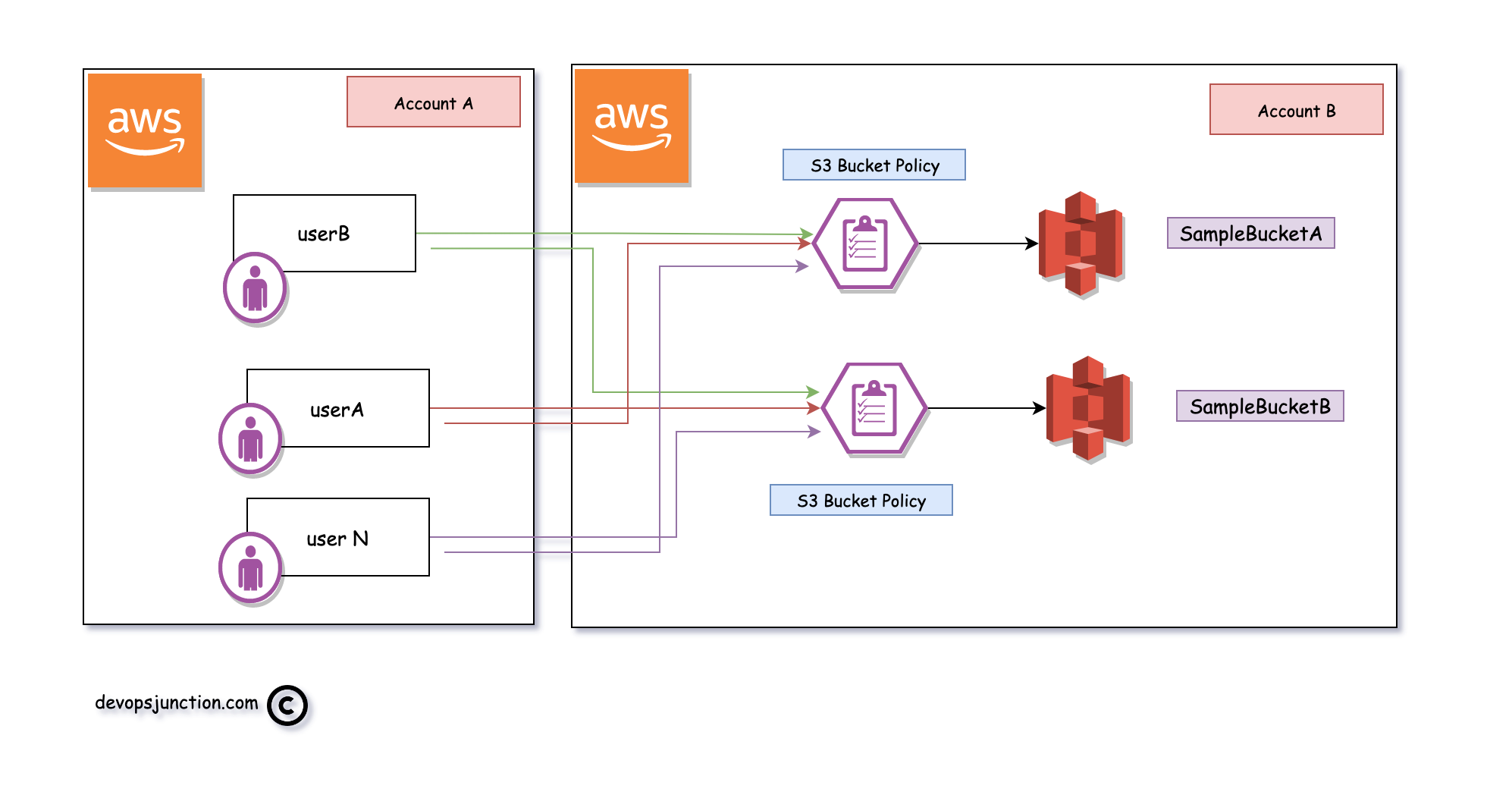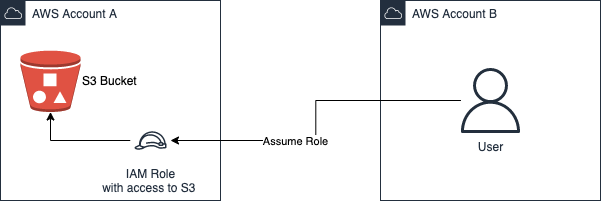
Transfer terabytes of data between AWS s3 buckets cross-account, cross-region and cross-vpc | by Ilyes Ajroud | ITNEXT

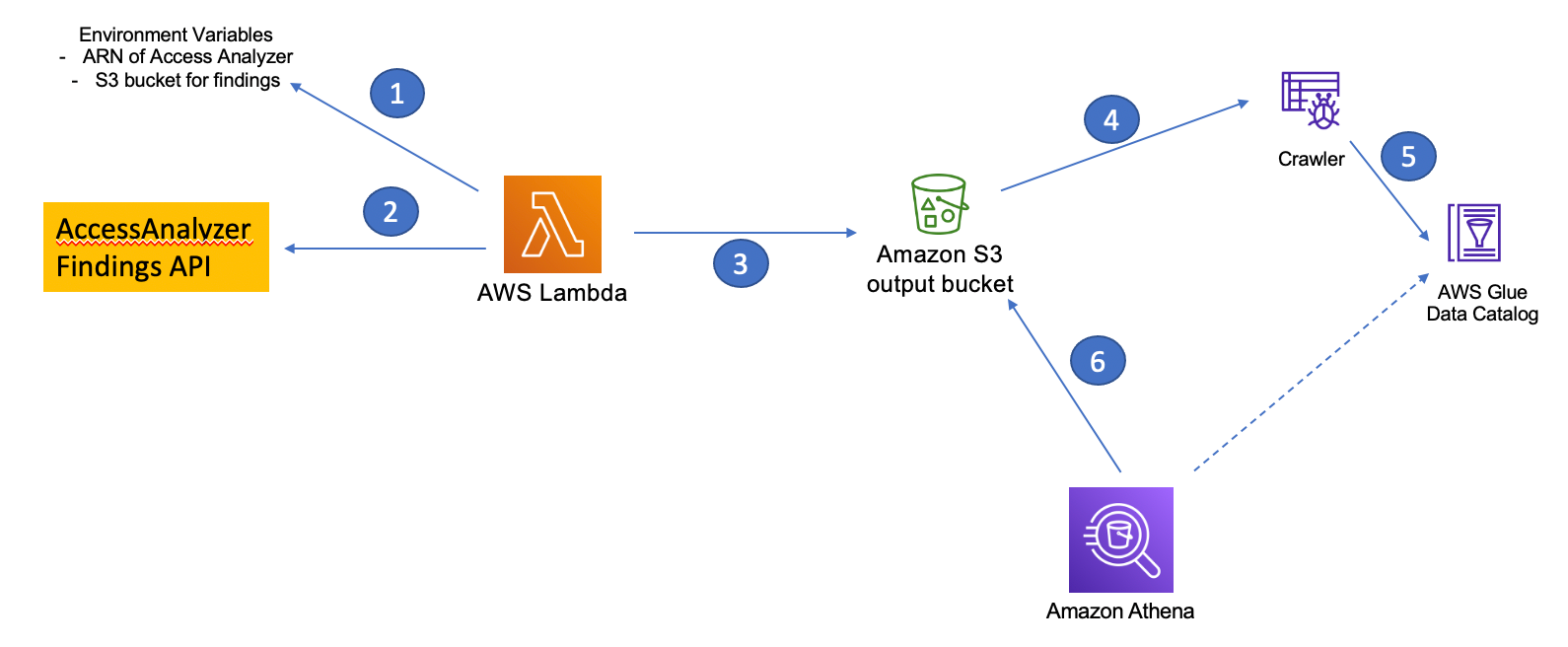
IAM makes it easier for you to manage permissions for AWS services accessing your resources | AWS Security Blog

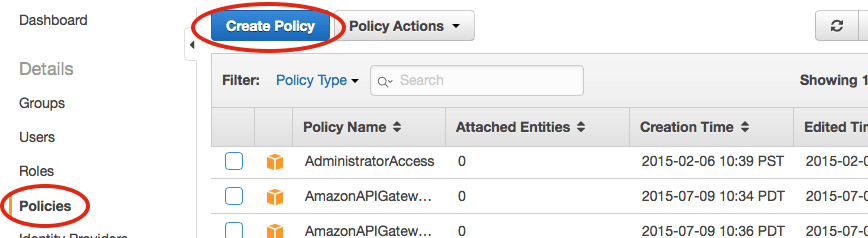
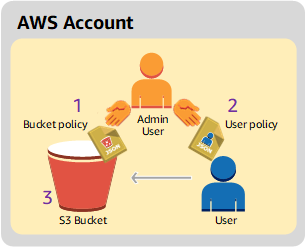
How to Use Bucket Policies and Apply Defense-in-Depth to Help Secure Your Amazon S3 Data | AWS Security Blog
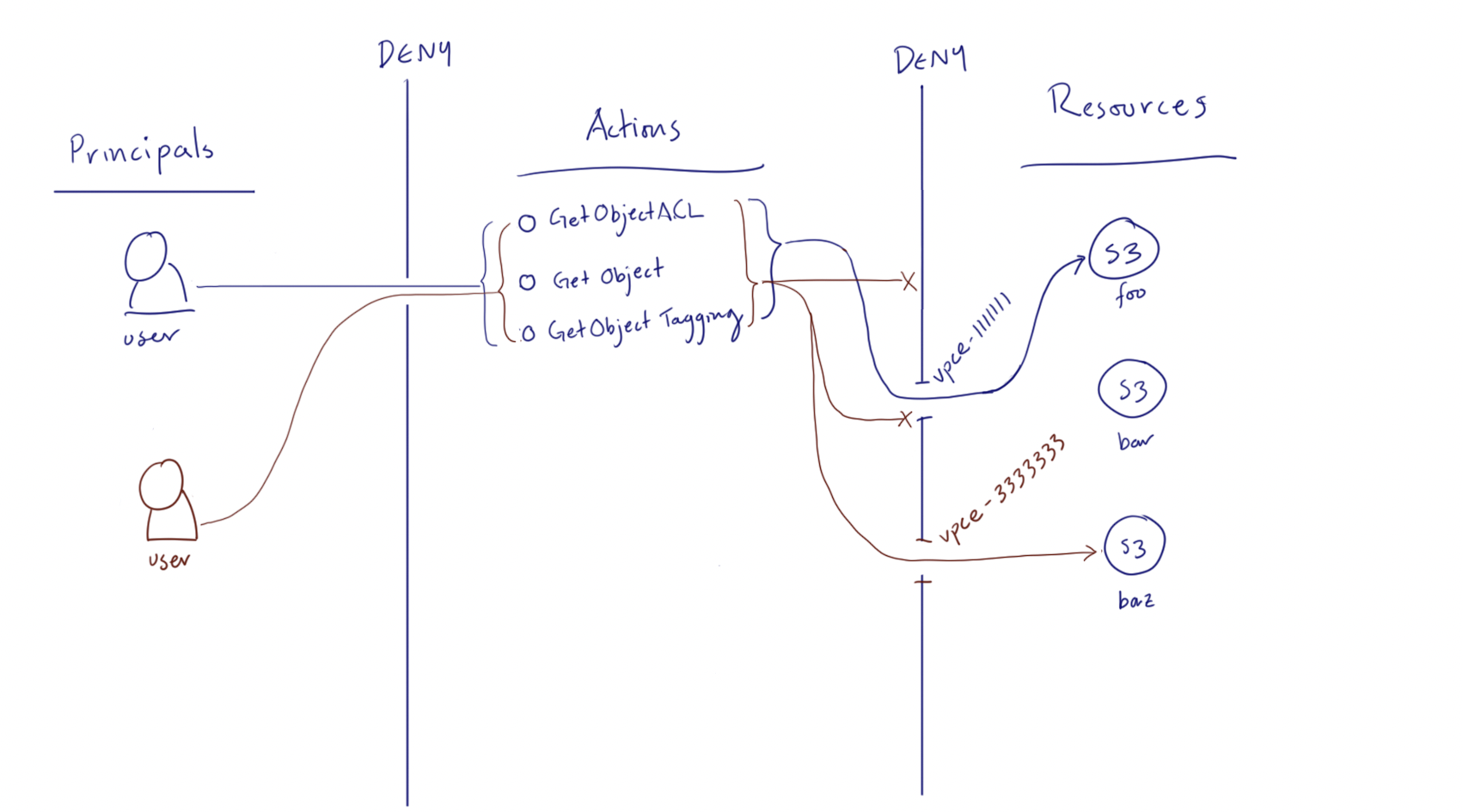
How to scale your authorization needs by using attribute-based access control with S3 | AWS Security Blog
How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

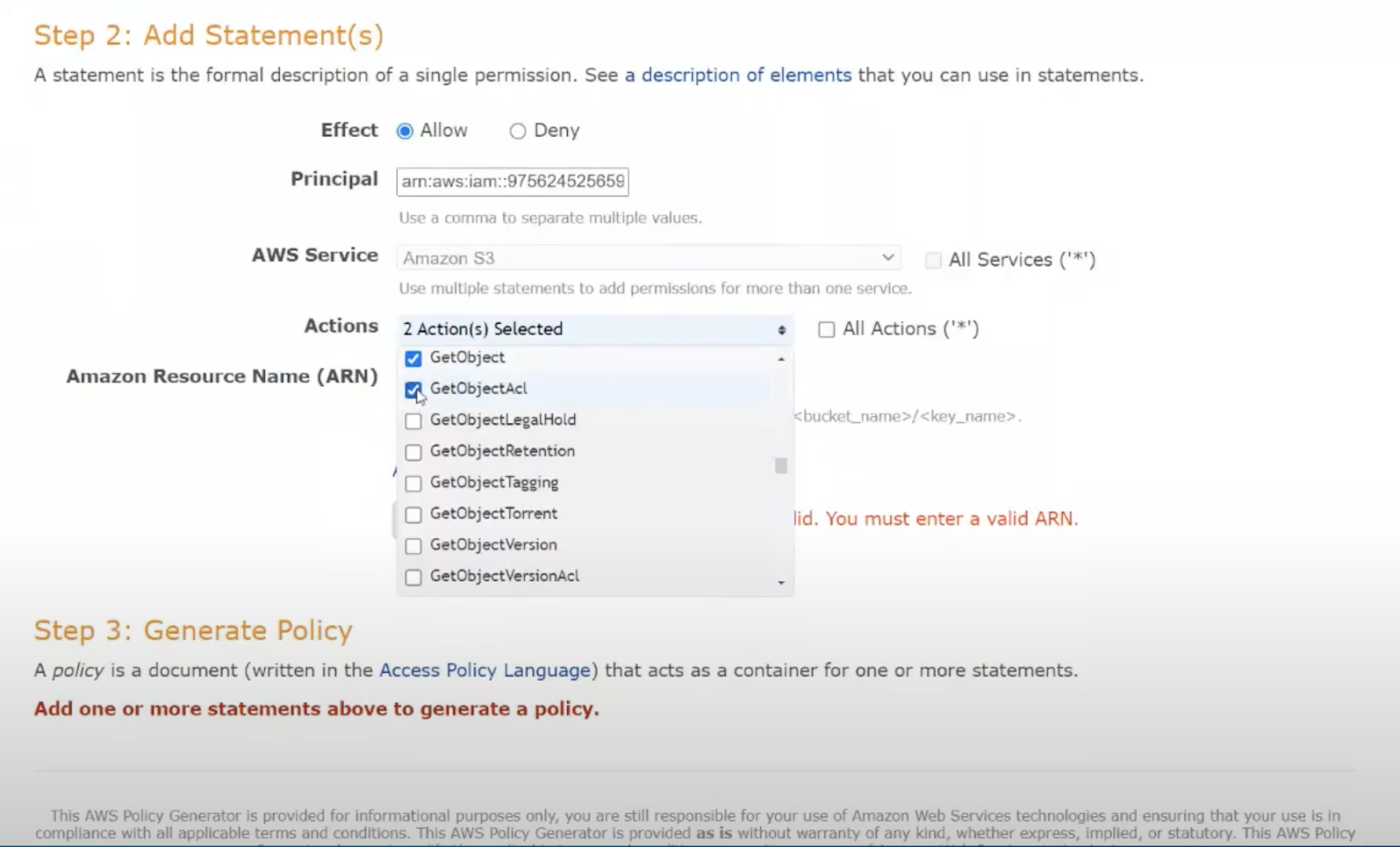
Sample S3 Bucket Policies. [Allowing only SSE-KMS based encrypted… | by Crishantha Nanayakkara | Medium