Identify unused IAM roles and remove them confidently with the last used timestamp | AWS Security Blog
Creating Zero Trust AWS Policies. ACM.36: Tools and techniques to create… | by Teri Radichel | Cloud Security | Medium

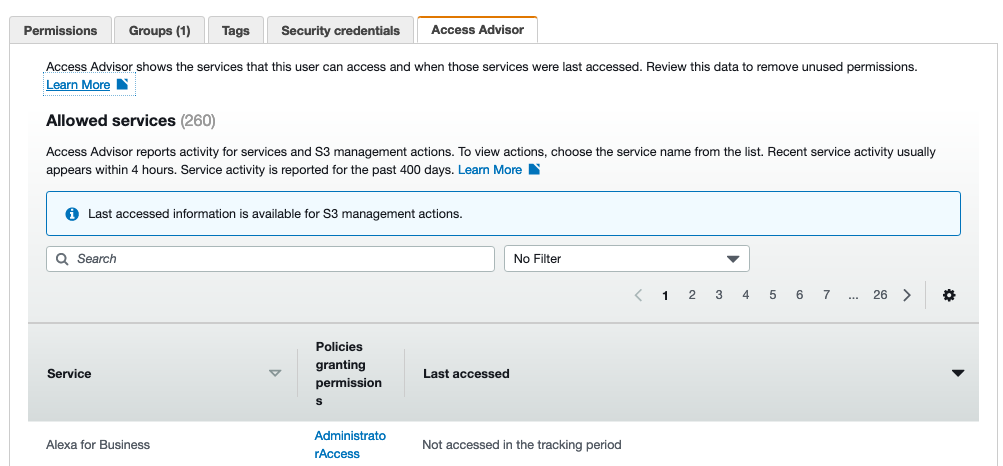
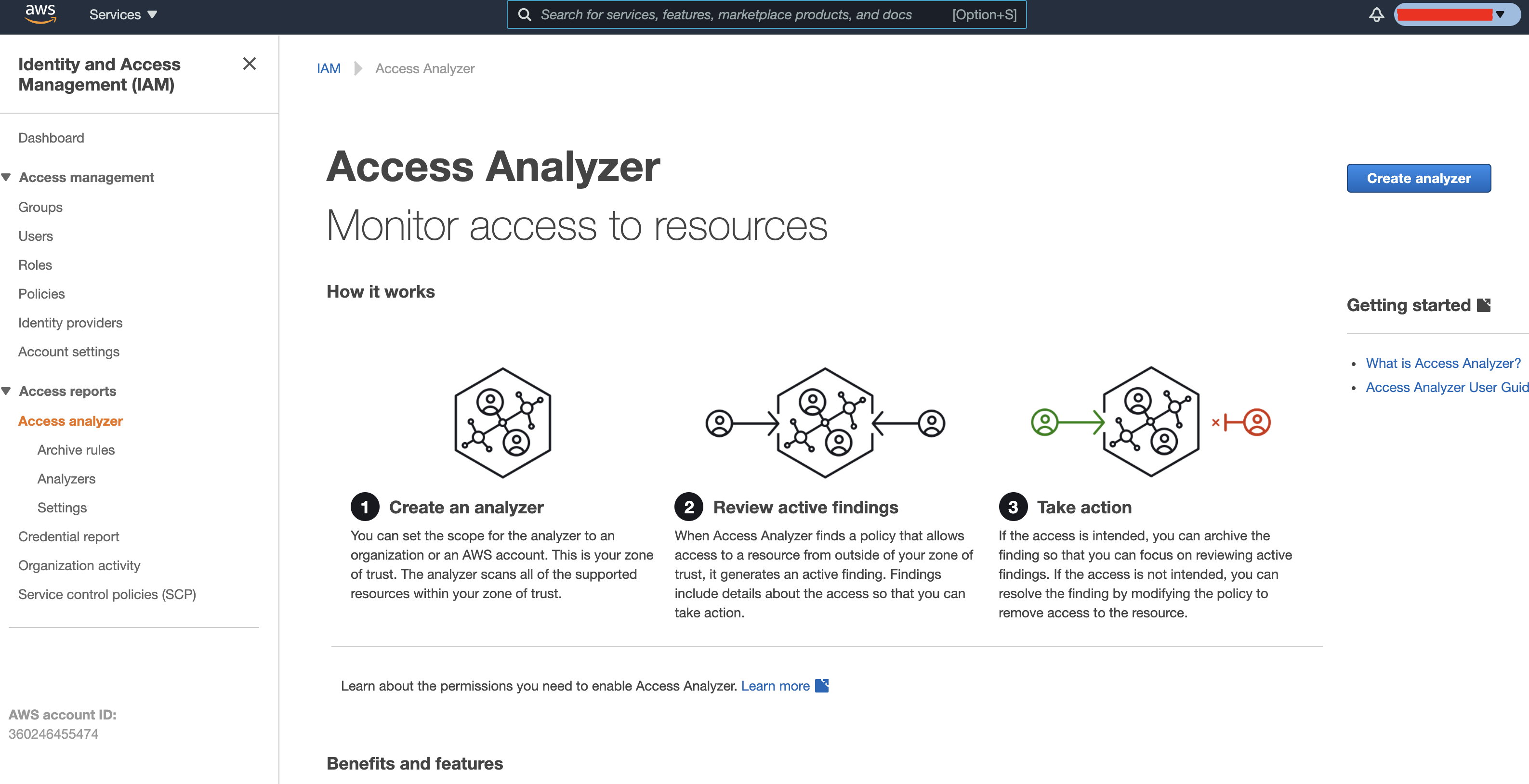
New! Set permission guardrails confidently by using IAM access advisor to analyze service-last-accessed information for accounts in your AWS organization | AWS Security Blog
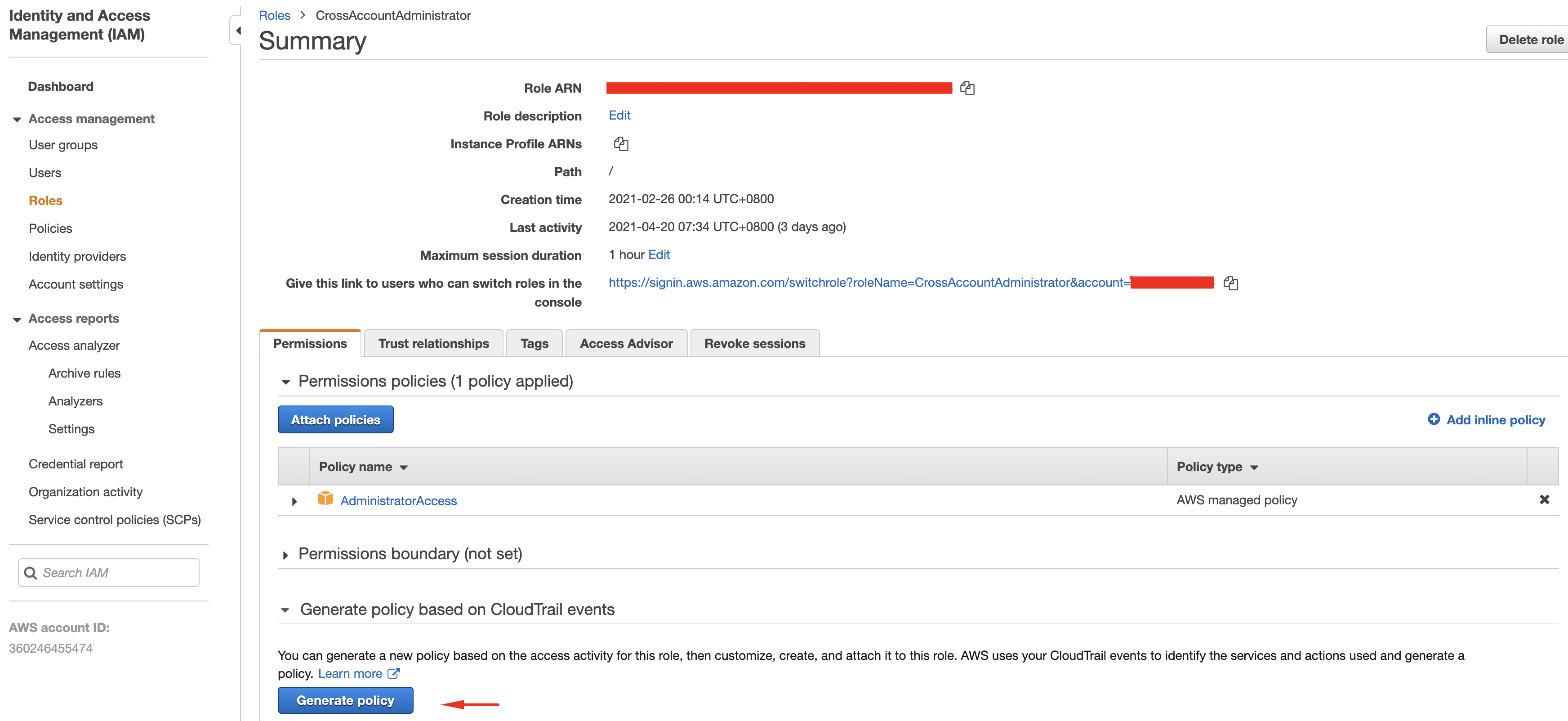
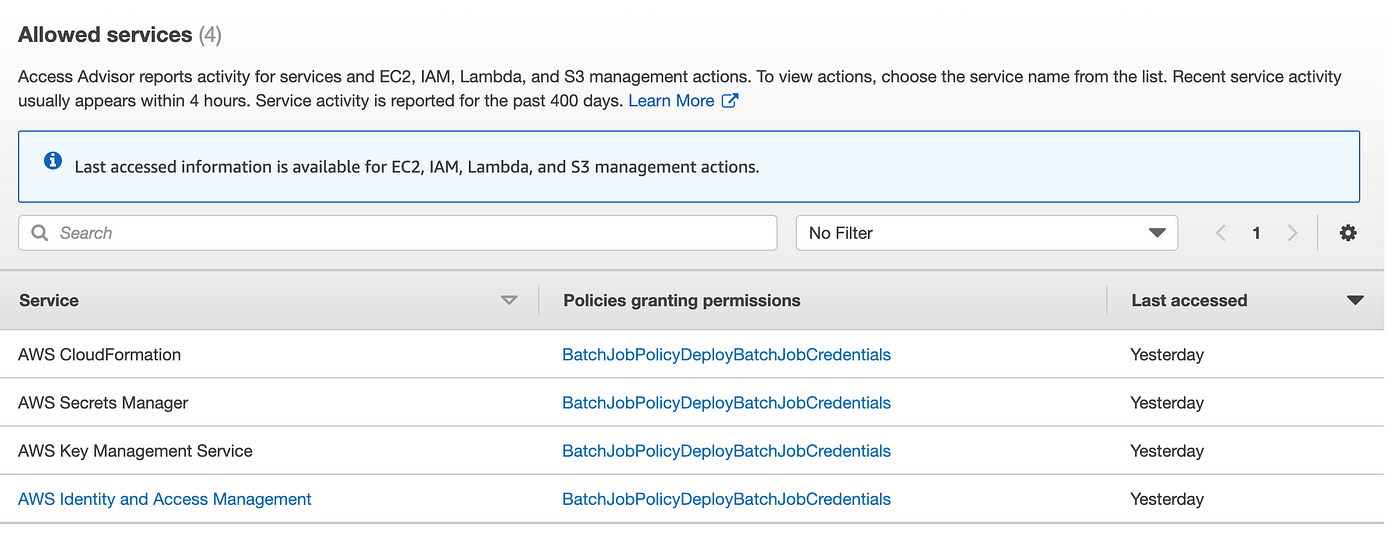
Building Least Privilege Policies with the AWS Policy Advisor - and a Demo with the Serverless Application Framework

Review last accessed information to identify unused EC2, IAM, and Lambda permissions and tighten access for your IAM roles | AWS Security Blog
Building Least Privilege Policies with the AWS Policy Advisor - and a Demo with the Serverless Application Framework








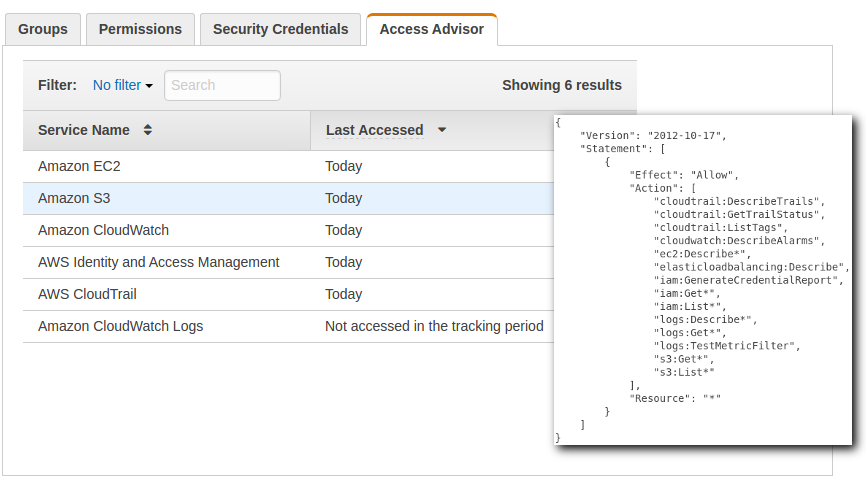



![Access Advisor - Mastering AWS Security [Book] Access Advisor - Mastering AWS Security [Book]](https://www.oreilly.com/api/v2/epubs/9781788293723/files/assets/5444f487-3c7d-4044-9bb7-228846fca50b.png)