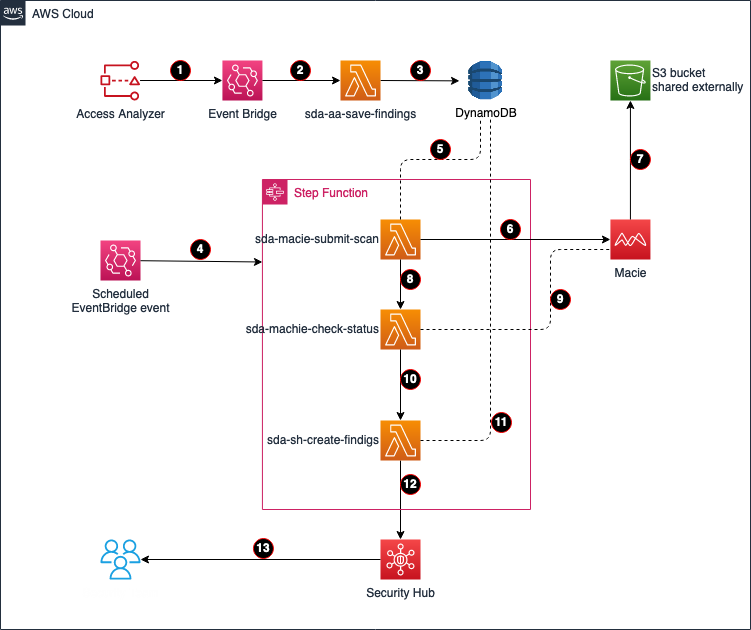
Enabling AWS IAM Access Analyzer on AWS Control Tower accounts | AWS Cloud Operations & Migrations Blog

Strengthening Security with IAM Access Analyzer & Amazon CloudFront Origin Access Control (OAC) | by Deniz Yilmaz | AWS Tip

Amazon Web Services on X: "RT @jeffbarr: #AWS IAM Access Analyzer Flags Unintended Access to S3 Buckets Shared Through Access Points - https://t.co/ZoQdefmOan https:/…" / X

IAM Access Analyzer makes it easier to implement least privilege permissions by generating IAM policies based on access activity | AWS Security Blog

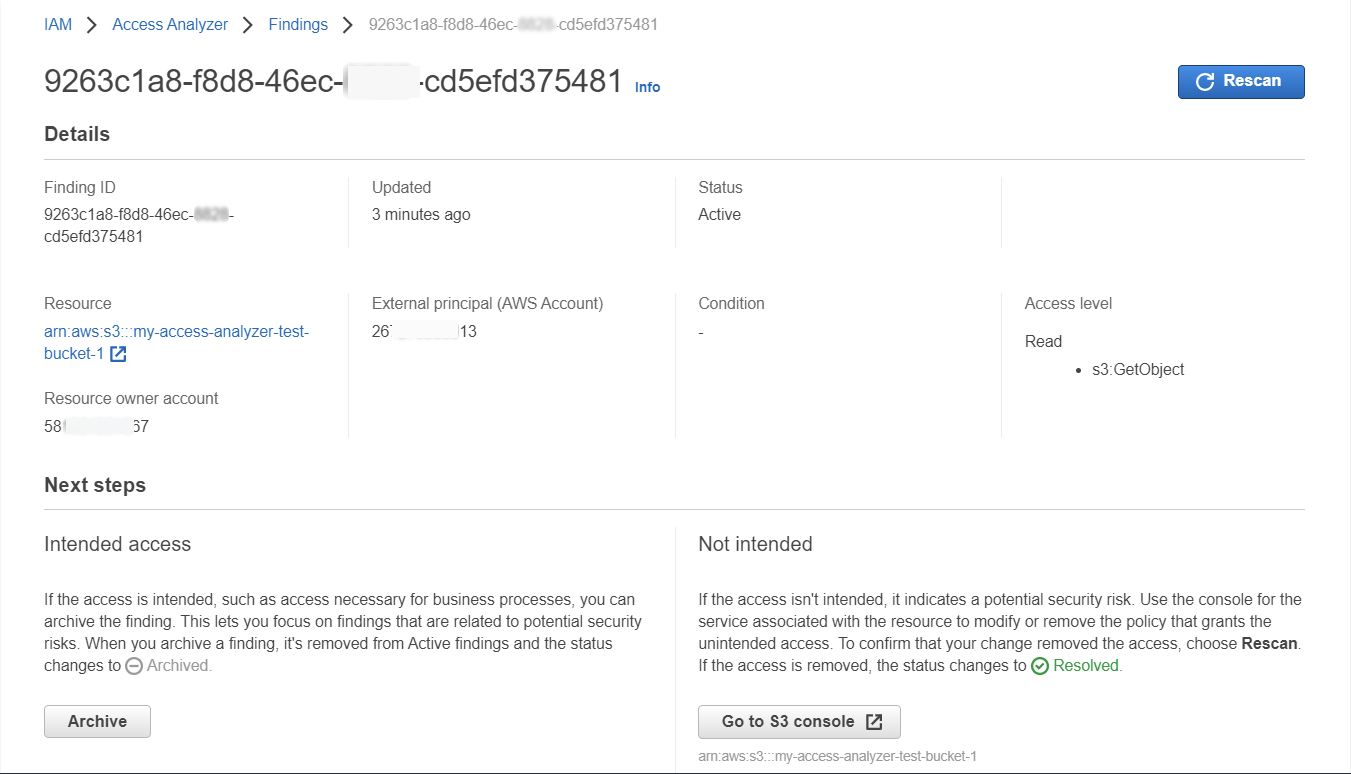
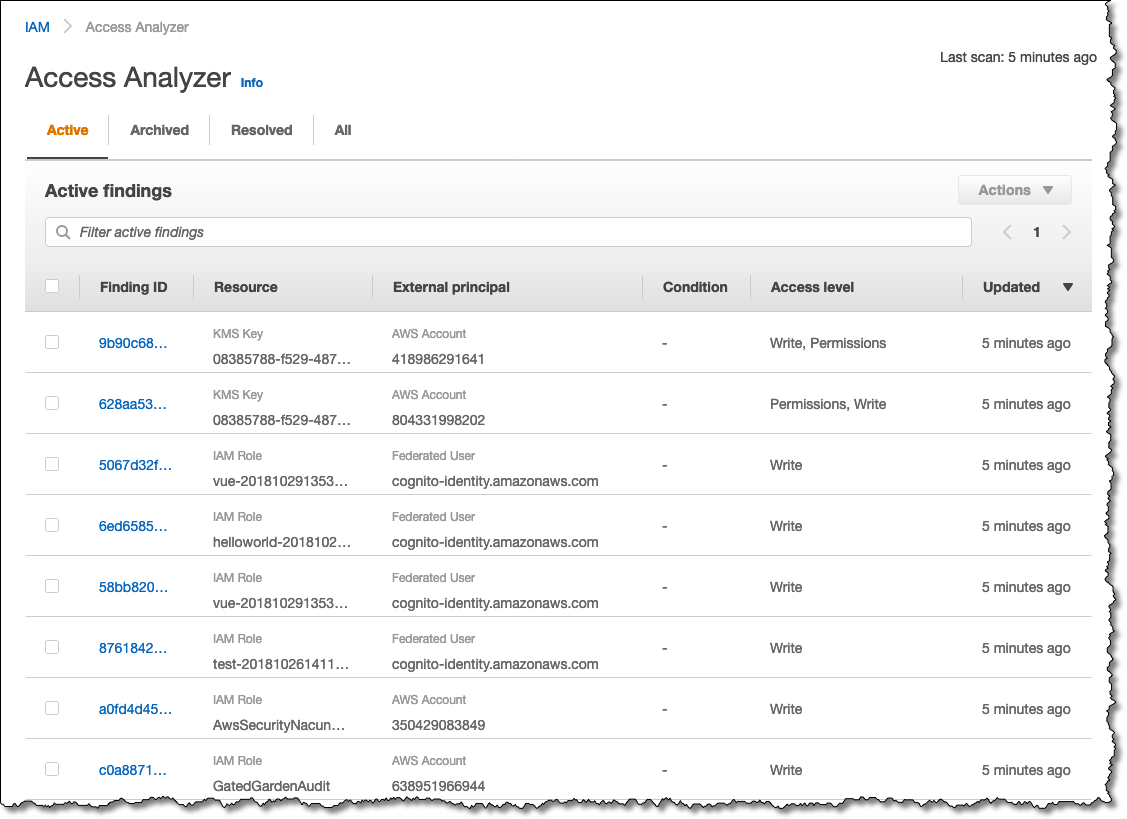
Identify Unintended Resource Access with AWS Identity and Access Management (IAM) Access Analyzer | AWS News Blog
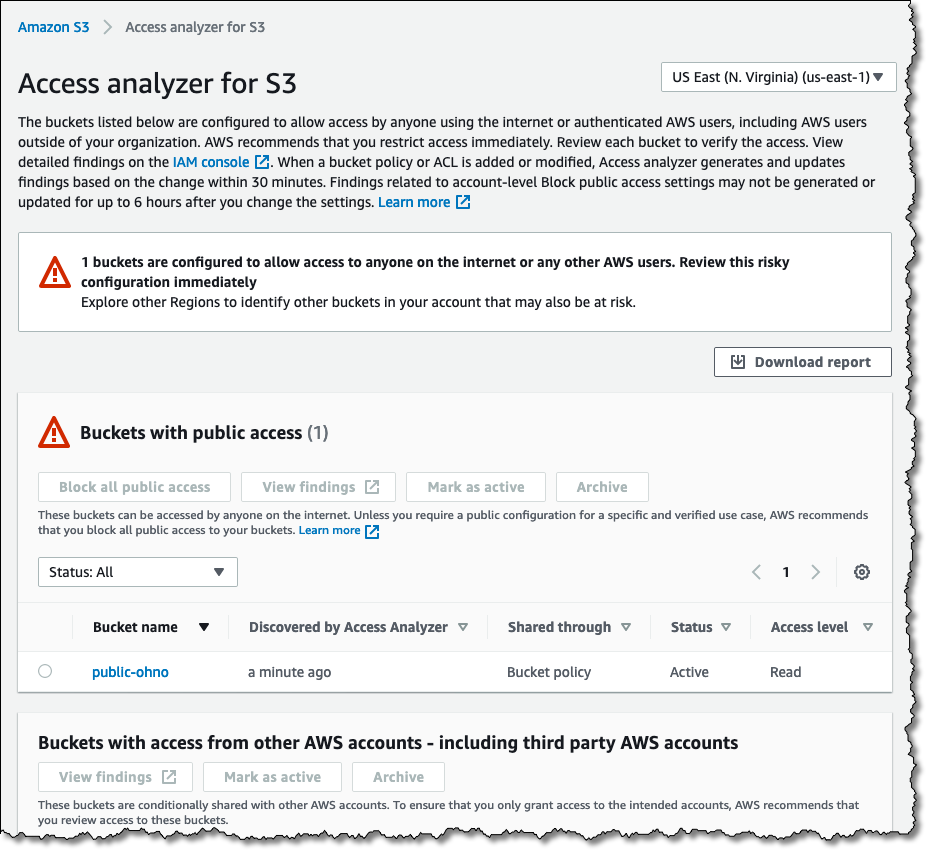
Identify Unintended Resource Access with AWS Identity and Access Management (IAM) Access Analyzer | AWS News Blog


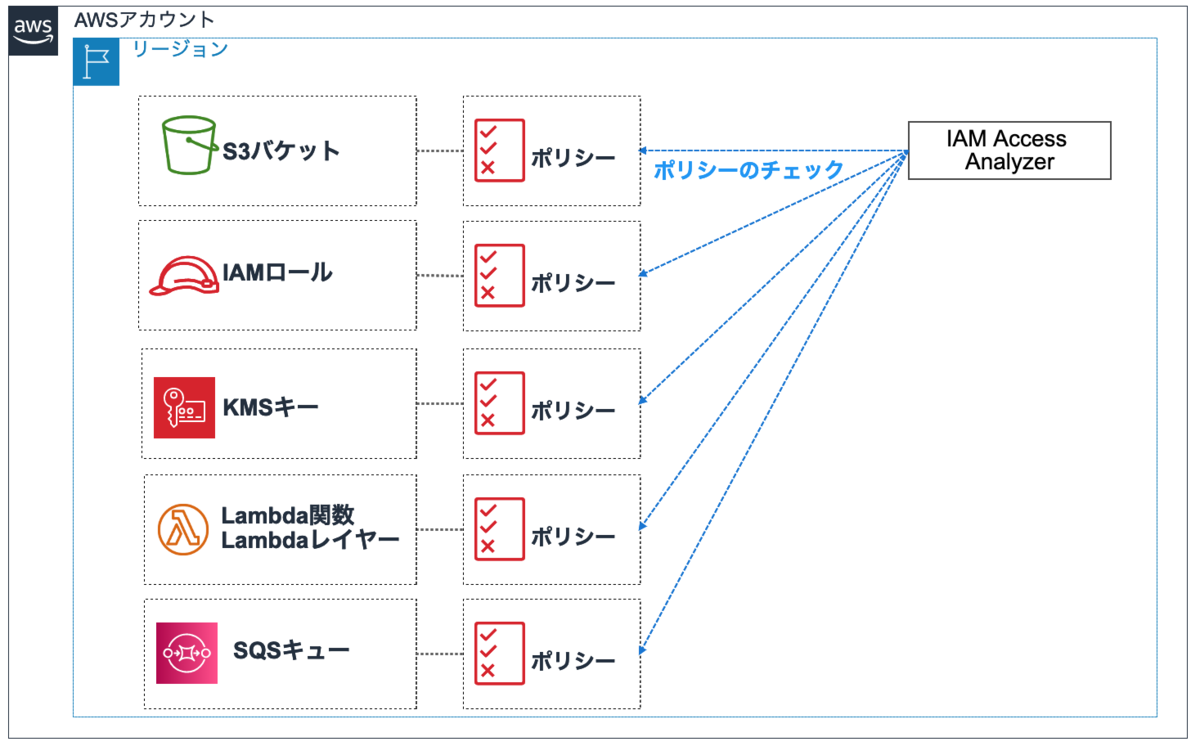
![アップデート] S3 バケットポリシー変更前に IAM Access Analyzer による「外部アクセス許可の検証」ができるようになりました! | DevelopersIO アップデート] S3 バケットポリシー変更前に IAM Access Analyzer による「外部アクセス許可の検証」ができるようになりました! | DevelopersIO](https://devio2023-media.developers.io/wp-content/uploads/2020/08/AWS-IAM-Access-Analyzer-1.png)