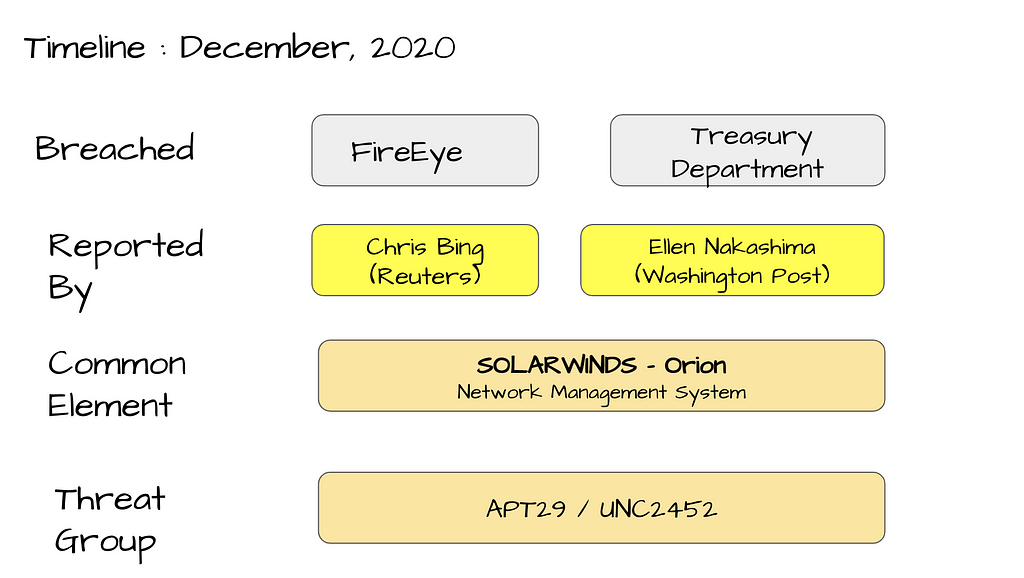
Visual Notes : SolarWinds Supply Chain compromise using SUNBURST backdoor (detected by FireEye) - Security Boulevard
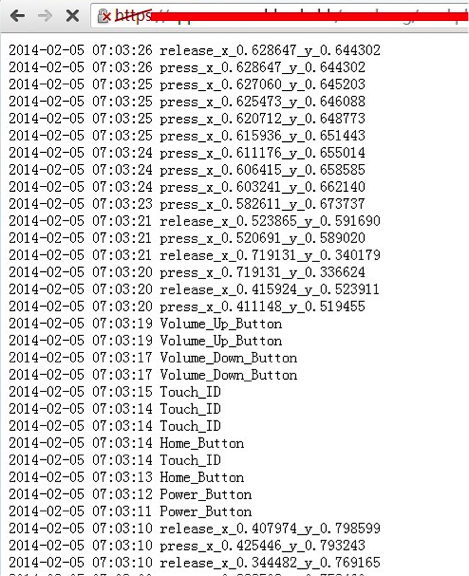
Security researchers highlight iOS flaw that enables hidden logging of touch events and other actions - 9to5Mac
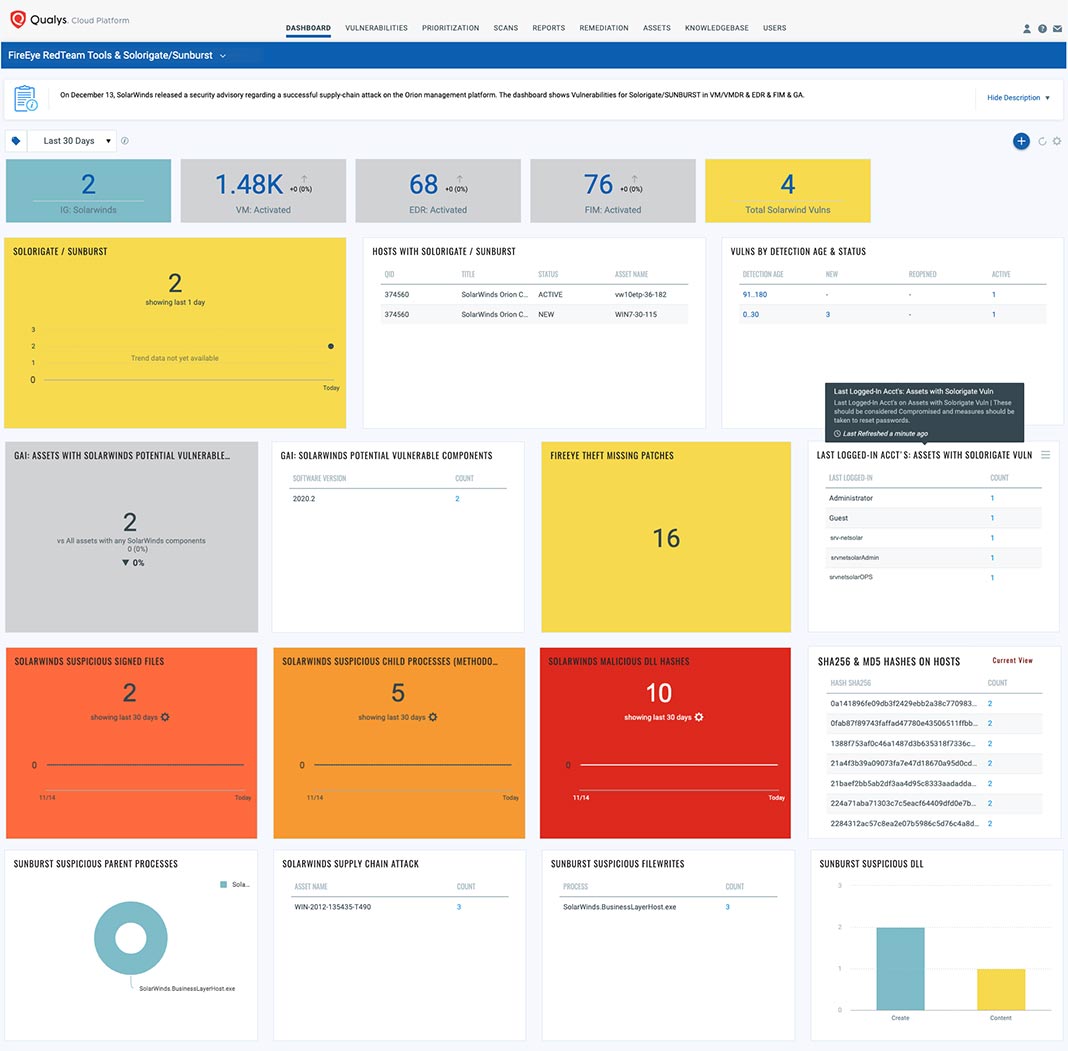
Qualys Researchers Identify 7+ Million Vulnerabilities Associated with SolarWinds / FireEye Breach by Analyzing Anonymized Vulnerabilities across Worldwide Customer Base

ExploitWareLabs - CARBANAK Week Part Three: Behind the CARBANAK Backdoor https://www.fireeye.com/blog/threat-research/2019/04/carbanak-week-part-three-behind-the-backdoor.html | Facebook

Abusing DLL Misconfigurations — Using Threat Intelligence to Weaponize R&D - Malware Analysis - Malware Analysis, News and Indicators