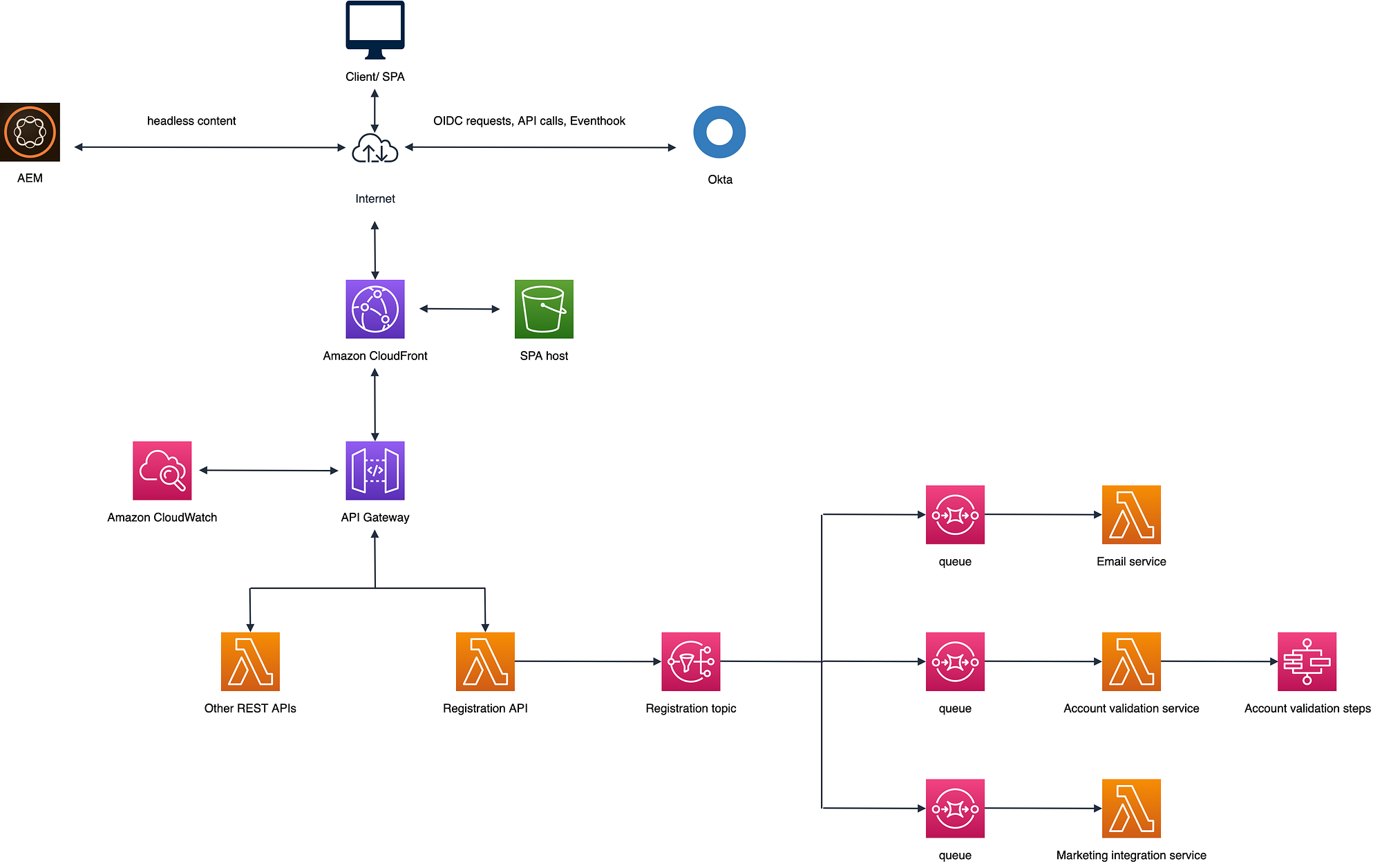
A Solution Overview and Architecture for an Okta Based Customer Identity and Access Management | by Eddie Yao | Medium

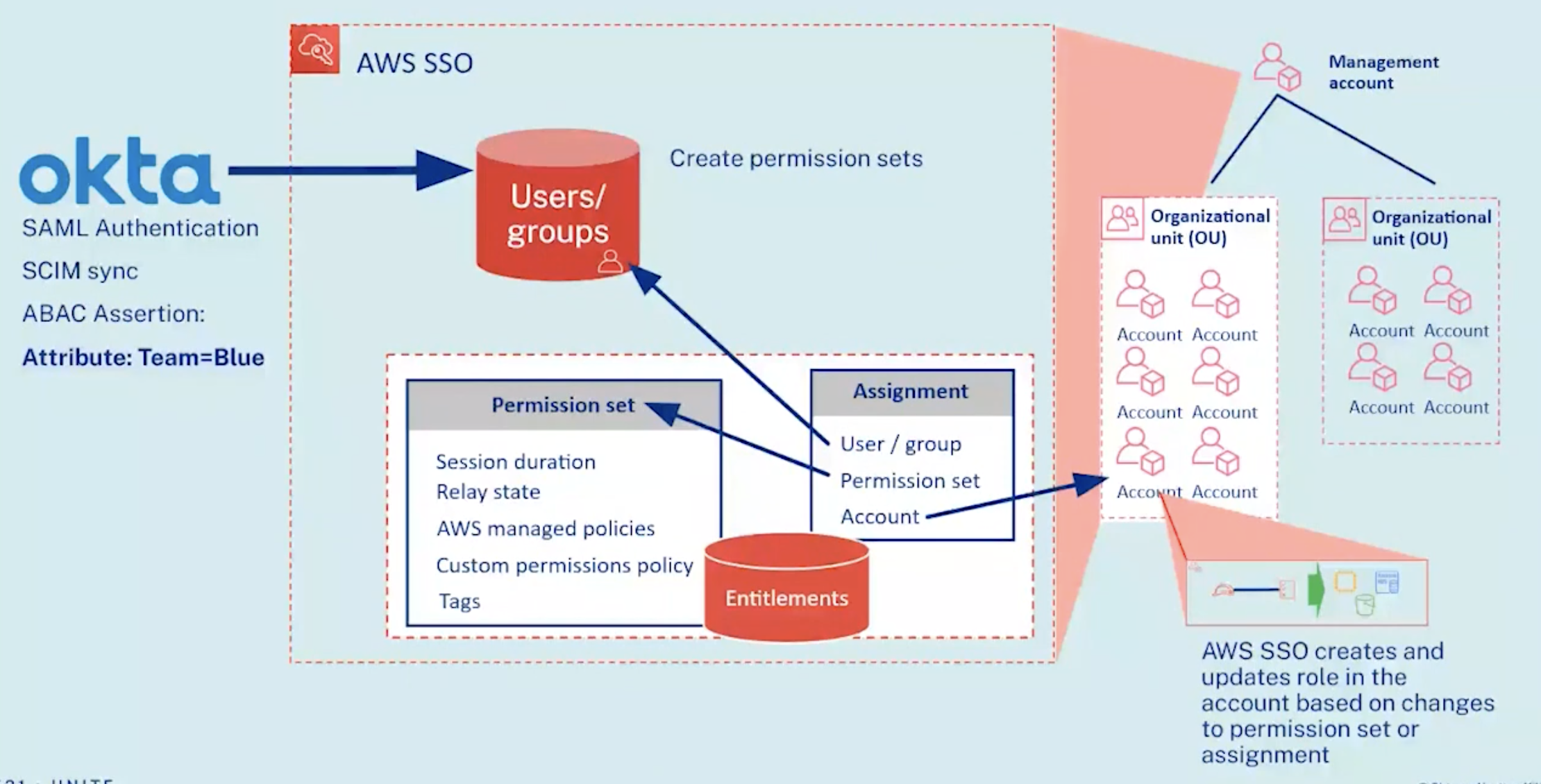
Build an end-to-end attribute-based access control strategy with AWS IAM Identity Center and Okta | AWS Security Blog

Securing AWS Access with Okta. In this guide we will break it down and… | by James Wu | Tubi Engineering
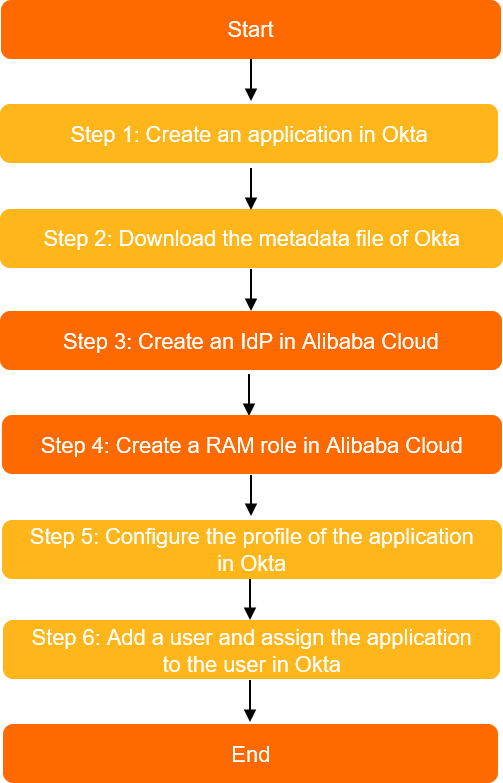
Implement role-based SSO from Okta - Resource Access Management - Alibaba Cloud Documentation Center

Build an end-to-end attribute-based access control strategy with AWS IAM Identity Center and Okta | AWS Security Blog

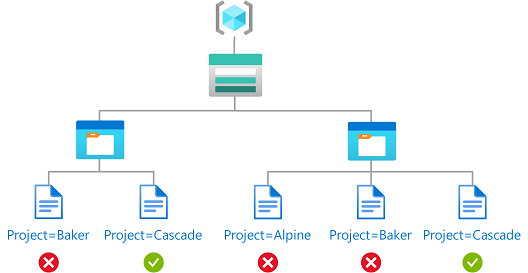
Securing Access Through Attribute-Based Access Control (ABAC) in AWS | by Rahul Grover | Slalom Build | Medium
Streamlining Snowflake Access Control: Empower Your Enterprise with Okta Workflow, Google Sheets, and Snowflake Default Role Management | by Deepam Kanjani | Snowflake | Medium